(Kali:
Lesson 5)
{ Fix bignum too big to
convert into `long' (RangeError) }
|
Section 0. Background
Information |
- Background information.
- The objective of the lesson is to show you
how to fix the RangeError when running older versions of Metasploit on a
32 bit Linux Operating System.
- Below is a typical error you might see when
running tools like msfconsole and msfvenom.
- /opt/metasploit/apps/pro/msf3/modules/payloads/stagers/android/reverse_tcp.rb:77:in
`not_after=': bignum too big to convert into
`long' (RangeError)
- Prerequisite
-
Lab Notes
- In this lab we will do the following:
- We will display RangeError
- We will make a backup of
reverse_tcp.rb
- We will adjust the calculation
for the cert.net_after
variable
- We will start of msfconsole
successfully
- Legal Disclaimer
- As a condition of your use of this Web
site, you warrant to computersecuritystudent.com that you will not use
this Web site for any purpose that is unlawful or
that is prohibited by these terms, conditions, and notices.
- In accordance with UCC § 2-316, this
product is provided with "no warranties, either express or implied." The
information contained is provided "as-is", with "no guarantee of
merchantability."
- In addition, this is a teaching website
that does not condone malicious behavior of
any kind.
- You are on notice, that continuing
and/or using this lab outside your "own" test environment
is considered malicious and is against the law.
- © 2020 No content replication of any kind
is allowed without express written permission.
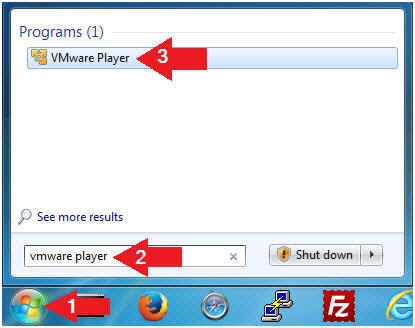
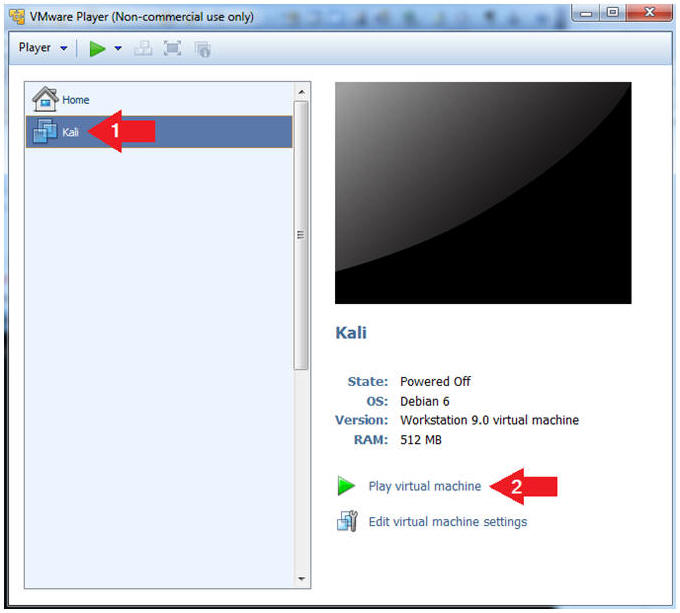
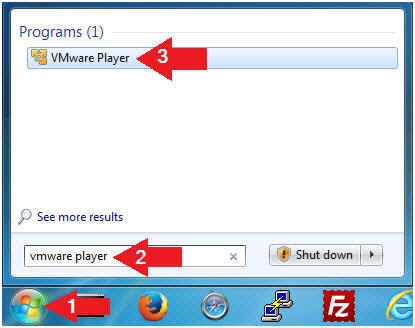
- Open VMware Player on your windows machine.
- Instructions:
- Click the Start Button
- Type "vmware player" in the search box
- Click on VMware Player
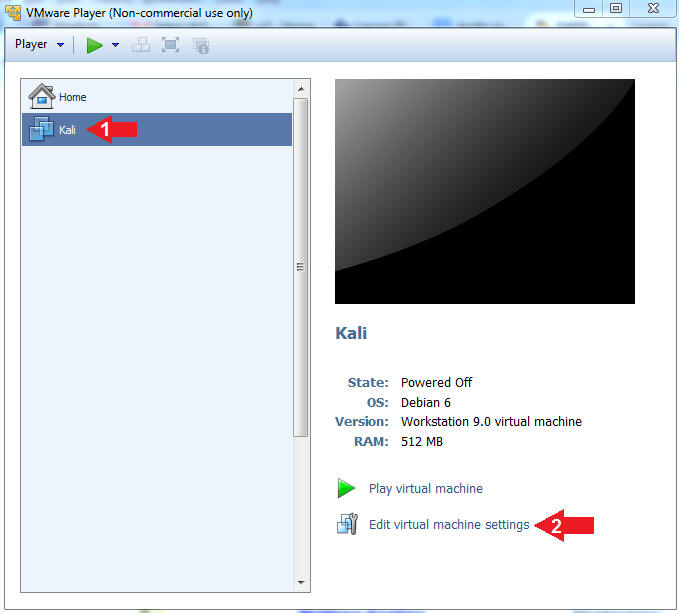
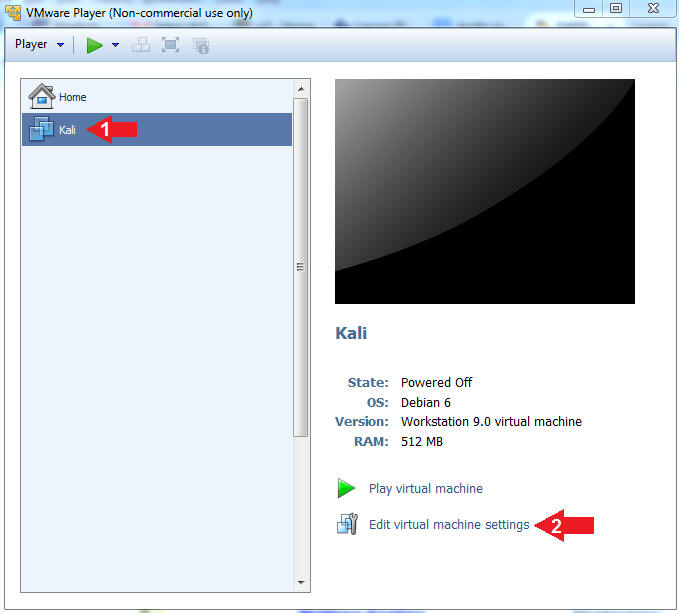
- Edit Virtual Machine Settings
- Instructions:
- Click on the Kali VM
- Click on Edit virtual machine settings
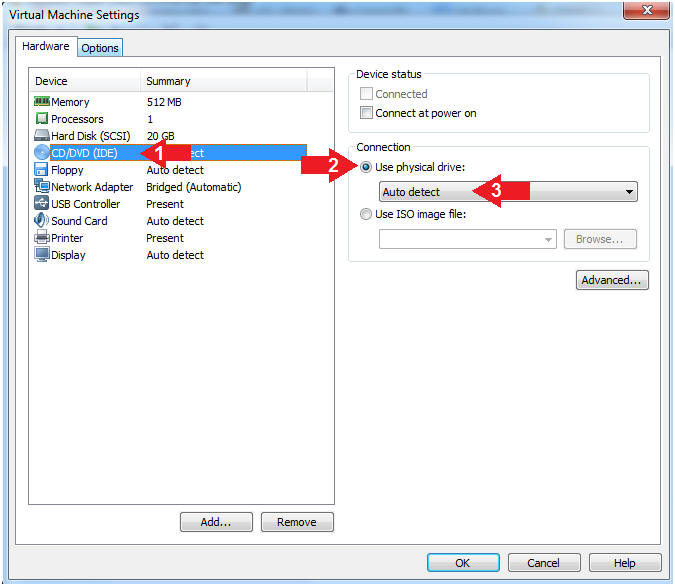
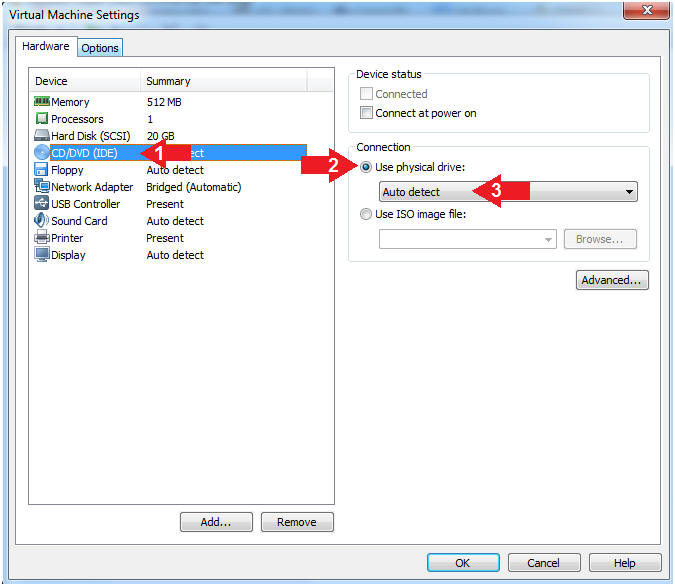
- Auto Detect Hard Drive
- Instructions:
- Click on CD/DVD(IDE)
- Click the Use physical drive: radio
button
- Make sure Auto detect is selected
- Edit Network Adapter
- Instructions:
- Highlight Network Adapter
- Select Bridged
- Click the OK Button
- Start the Kali VM
- Instructions:
- Click on the Kali VM
- Click on Play virtual machine
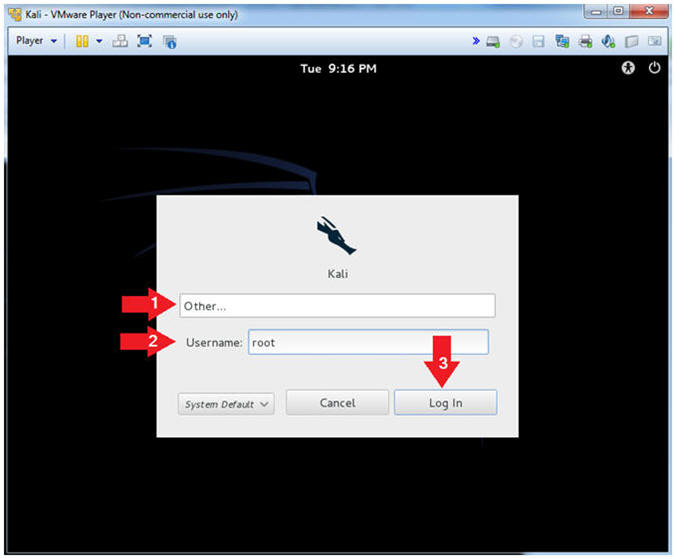
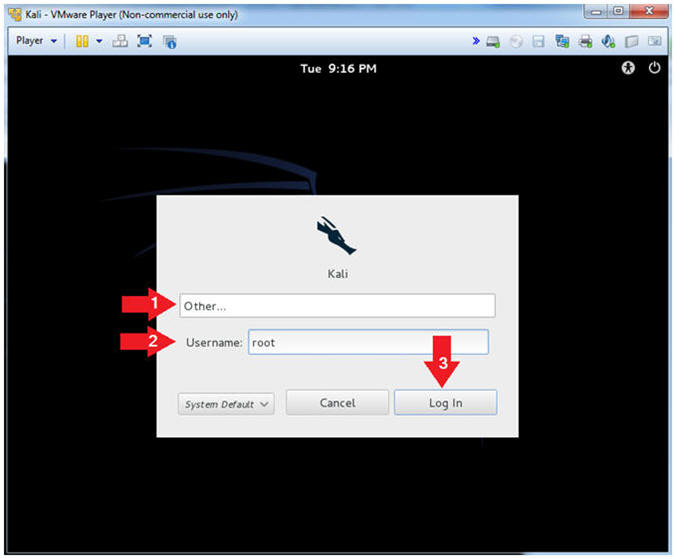
- Supply Username
- Instructions:
- Click Other
- Username: root
- Click the Login Button
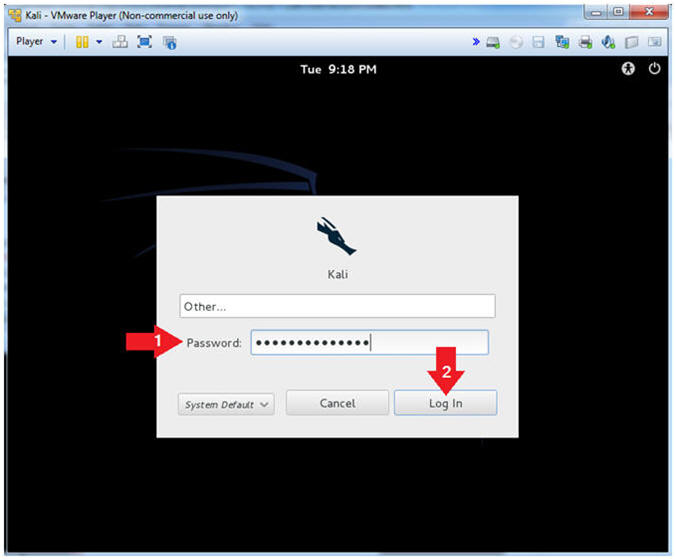
- Supply Password
- Instructions:
- Password: Provide the root password
- Click the Login Button
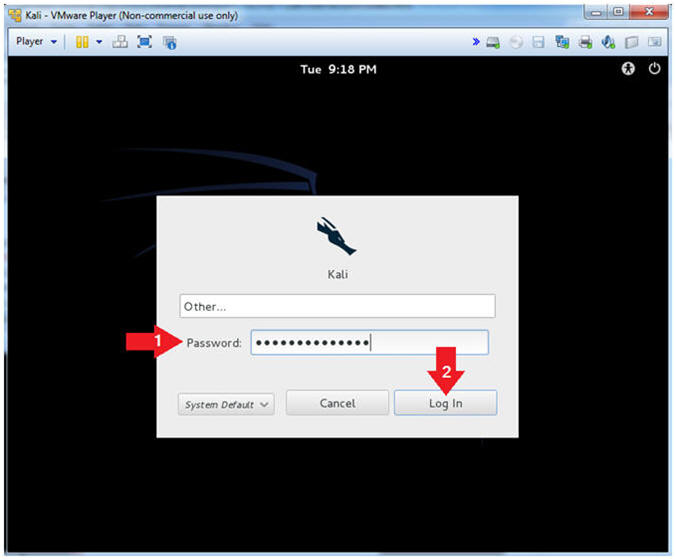
|
Section 3. Obtain IP Address Address |
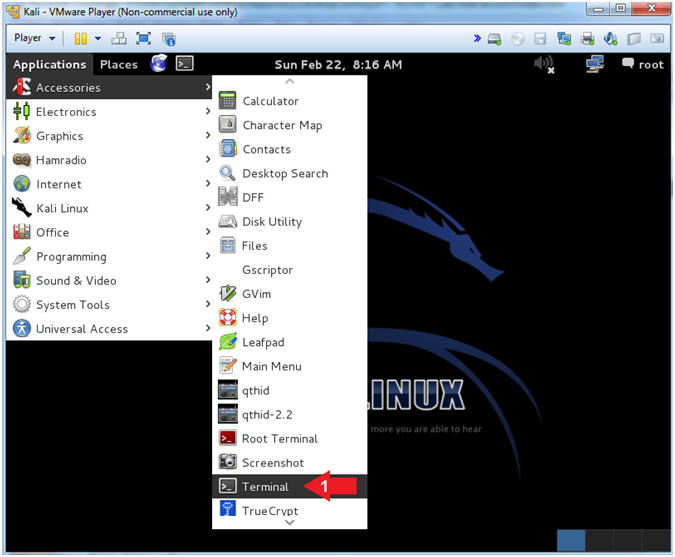
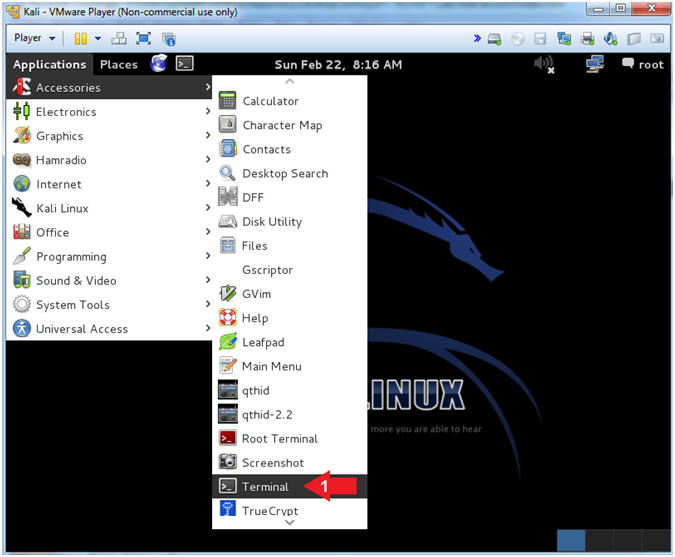
- Open a Terminal
- Instructions:
- Applications --> Accessories -->
Terminal
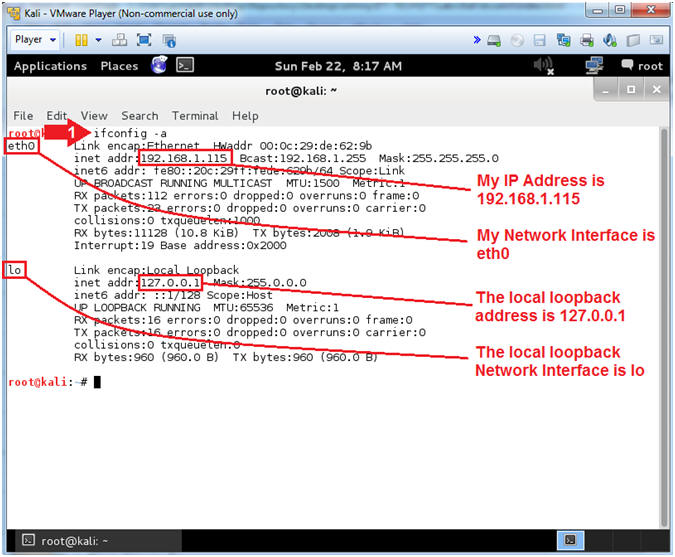
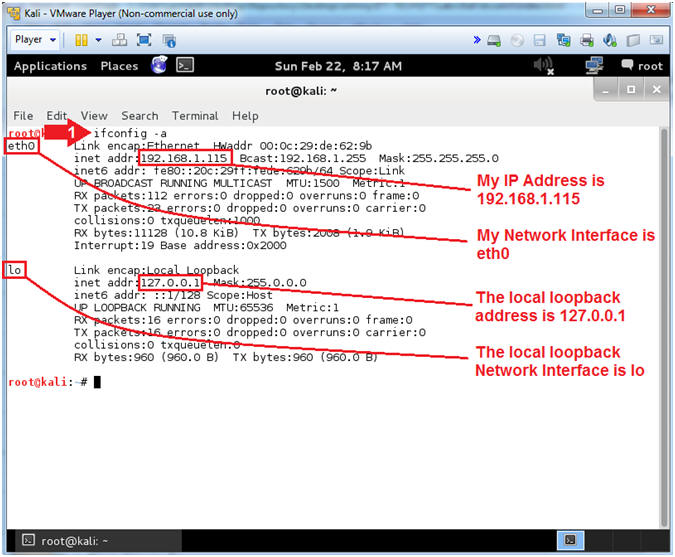
- Get IP Address
- Instructions:
- ifconfig -a
- Notes (FYI):
- As indicated below, my IP address is
192.168.1.115 for Network Interface eth0.
- Please record your IP address
- The Local Loopback Address is 127.0.0.1
for Network Interface lo.
- The loopback device is a special,
virtual network interface that your computer uses to communicate
with itself. When the network or wifi is disconnected the
loopback exists so applications running on your computer can
always connect to servers on the same machine.
|
Section 4. Start
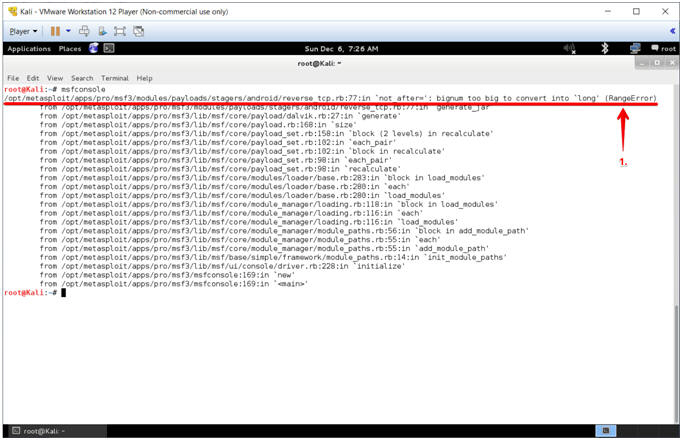
msfconsole and View RangeError |
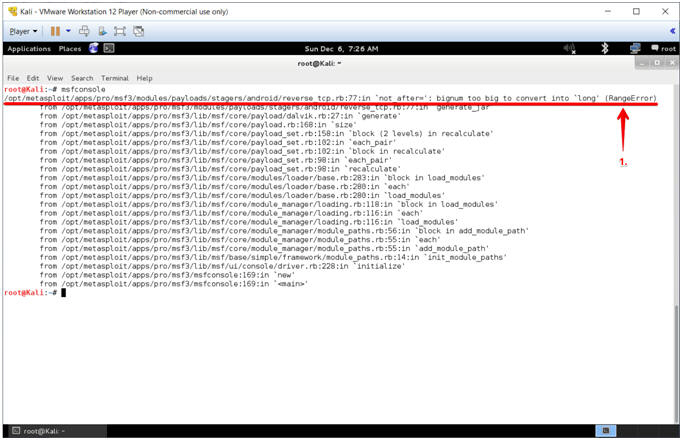
- msfconsole RangeError
- Instructions:
- Notice the RangeError produced by
reverse_tcp.rb
- Note(FYI):
-
/opt/metasploit/apps/pro/msf3/modules/payloads/stagers/android/reverse_tcp.rb:77:in
`not_after=': bignum too big to convert into
`long' (RangeError)
- This is because the value for the
cert.net_after variable in reverse_tcp.rb exceeded
2,147,483,648.
|
Section 5. Fix
msfconsole RangeError |
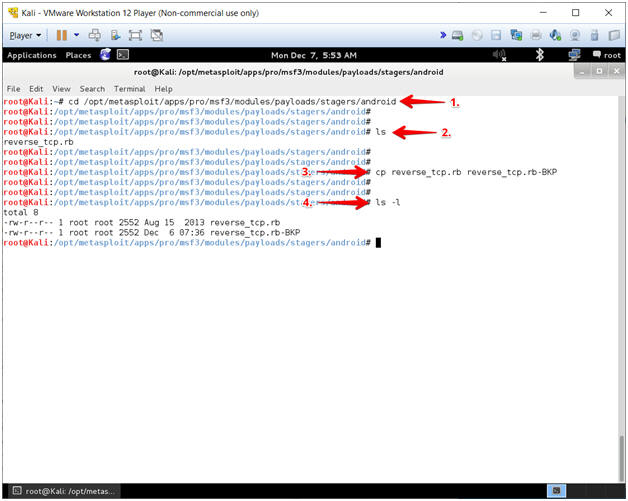
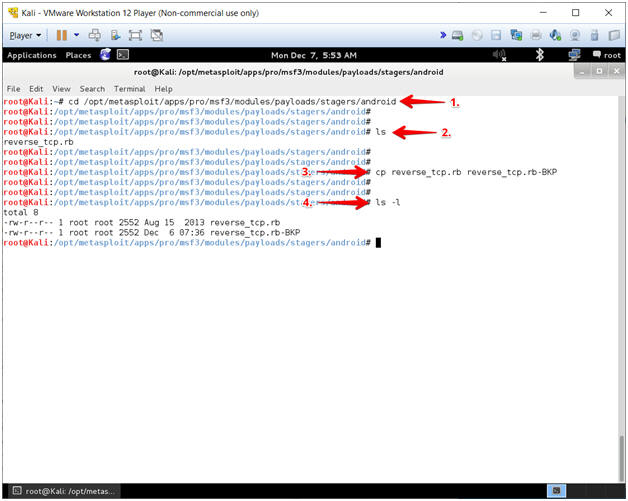
- Make Backup Copy of reverse_tcp.rb
- Instructions:
- cd
/opt/metasploit/apps/pro/msf3/modules/payloads/stagers/android
- ls
- cp reverse_tcp.rb reverse_tcp.rb-BKP
- ls -l
- Note(FYI):
- Command #1, Use (cd) to change
directory to (/opt/metasploit/apps/pro/msf3/modules/payloads/stagers/android).
- Command #2, Use (ls) to list the
contents of the current directory.
- Command #3, Use (cp) to make a copy of
the (reverse_tcp.rb)
file.
- Command #4, Use (ls -l) to long list
the contents of the current directory.
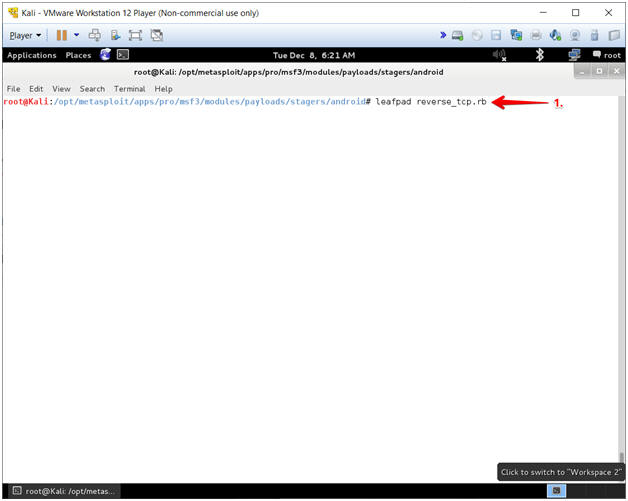
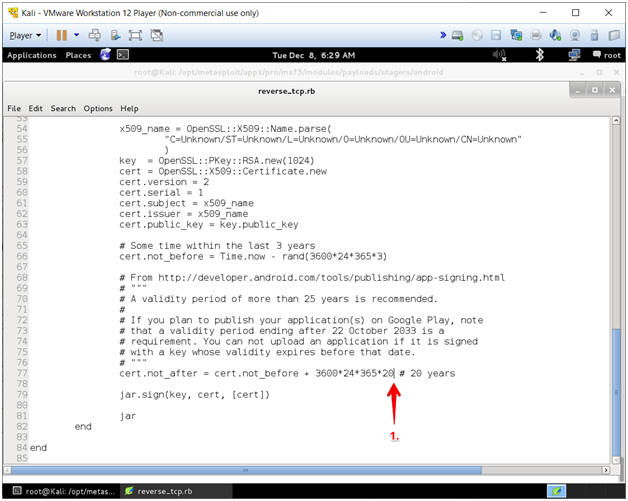
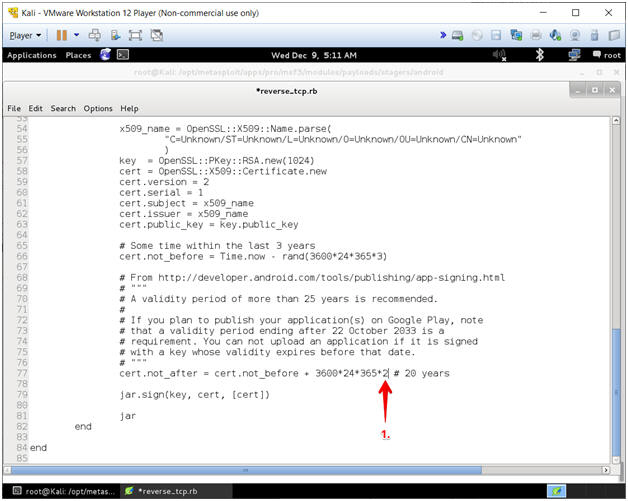
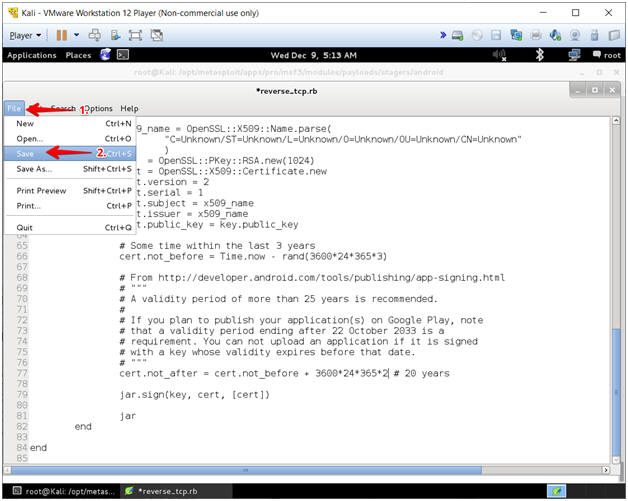
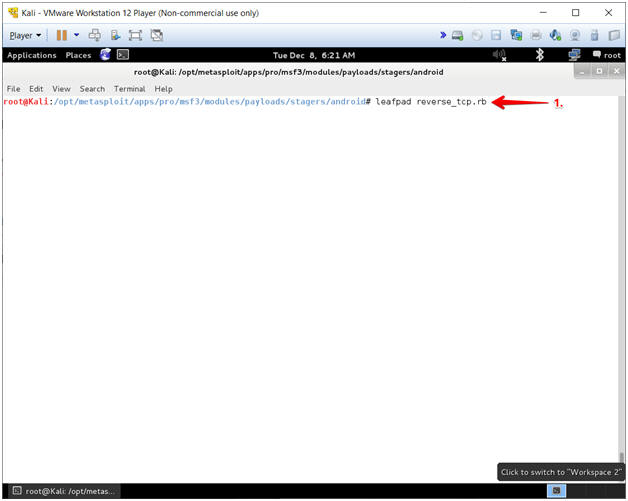
- Open reverse_tcp.rb
- Instructions:
- leafpad reverse_tcp.rb
- Note(FYI):
- Command #1, Use the text editor (leafpad)
to open the following file (reverse_tcp.rb).
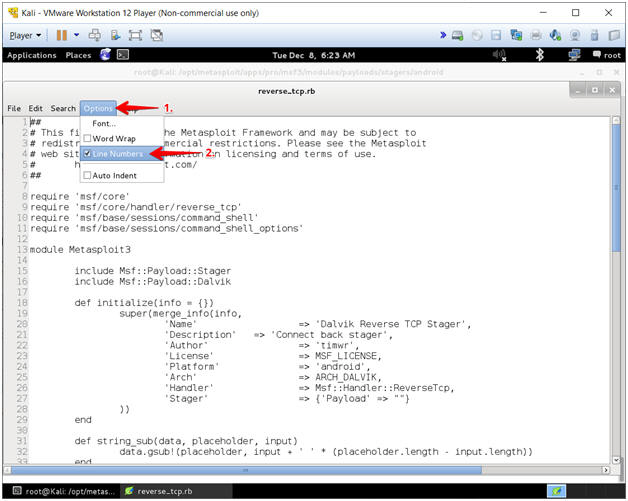
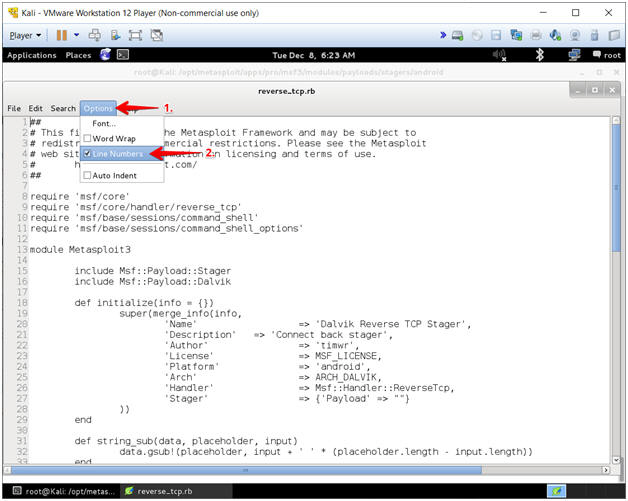
- Enable Line Numbers
- Instructions:
- Select Options
- Click on Line Numbers
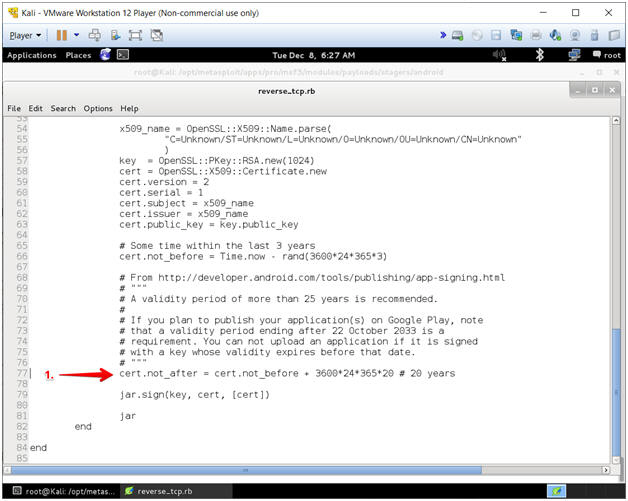
- Go To Line 77
- Instructions:
- Arrow Down to Line 77
- Note(FYI):
- The Cursor should be on the same line
as cert.net_after
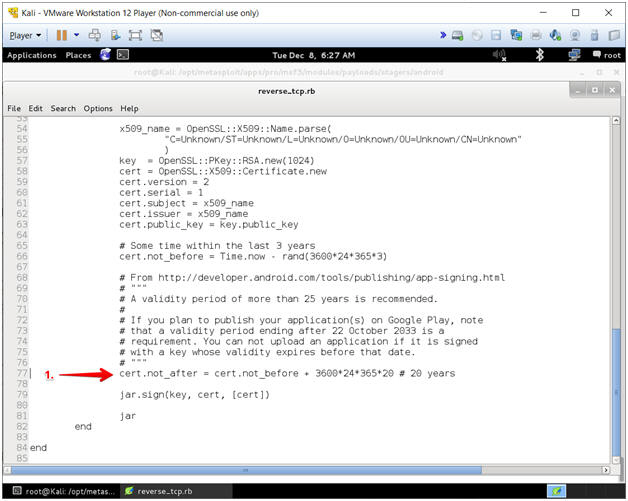
- Cursor Over
- Instructions:
- Cursor over to the position immediately
after the first number
20.
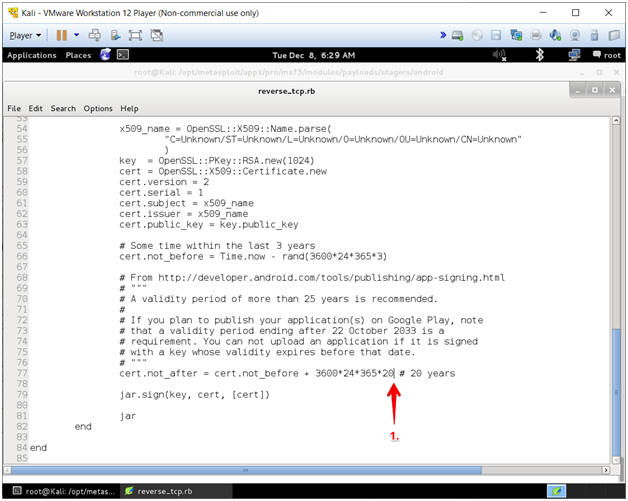
- Delete Trailing Zero
- Instructions:
- Press the <Backspace> key to delete the
"0" at the end of the number 20 to create the number 2.
- Note(FYI):
- The new number should be 2.
- In ruby, the bignum data type goes up
to
2,147,483,648.
-
The bignum data types range (2,147,483,648)
is exceeded, when the value of (cert.not_before) is added to
(3600*24*365*20).
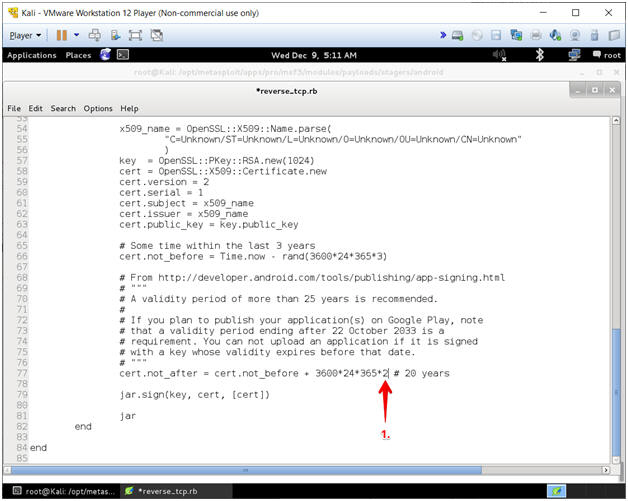
- Save File
- Instructions:
- Select File
- Select Save
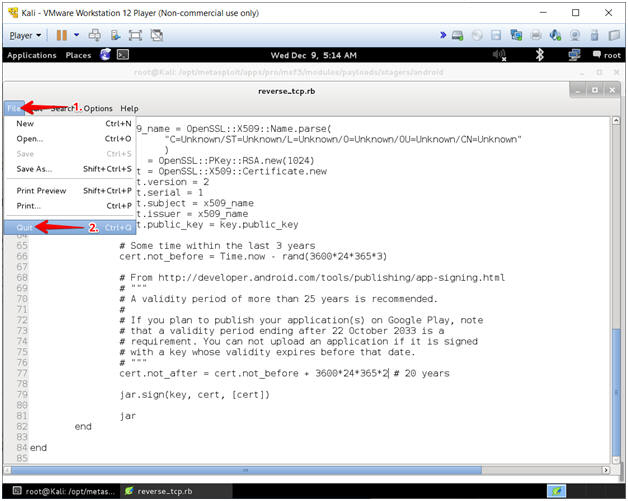
- Close File
- Instructions:
- Select File
- Select Quit
|
Section 6. Start
msfconsole successfully |
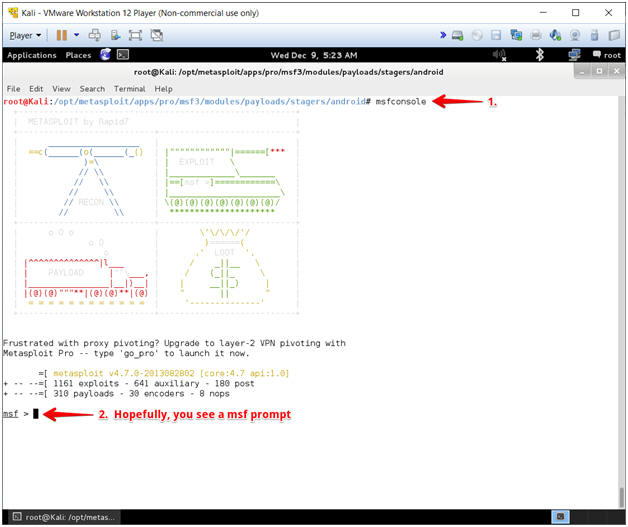
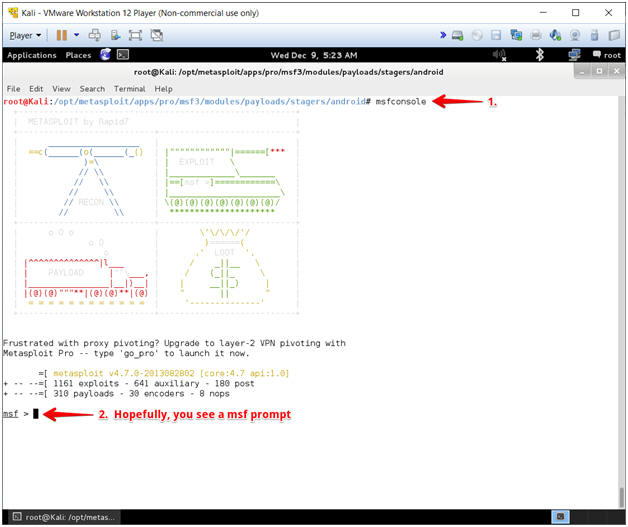
- Start Metasploit Console (msfconsole)
- Instructions:
- msfconsole
- You should now see a Metasploit banner
and "msf >" prompt.
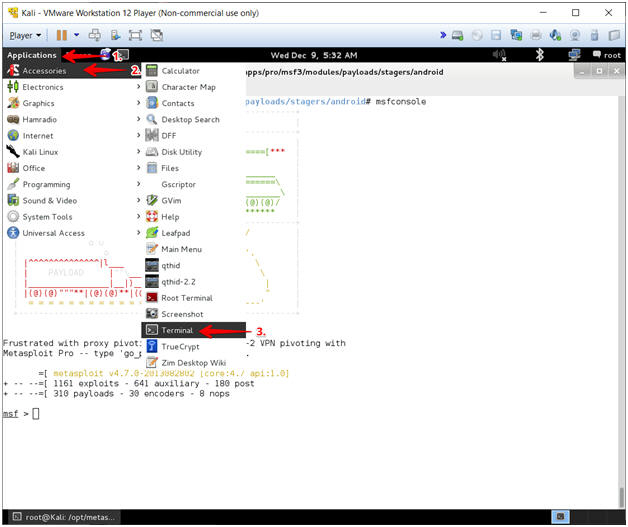
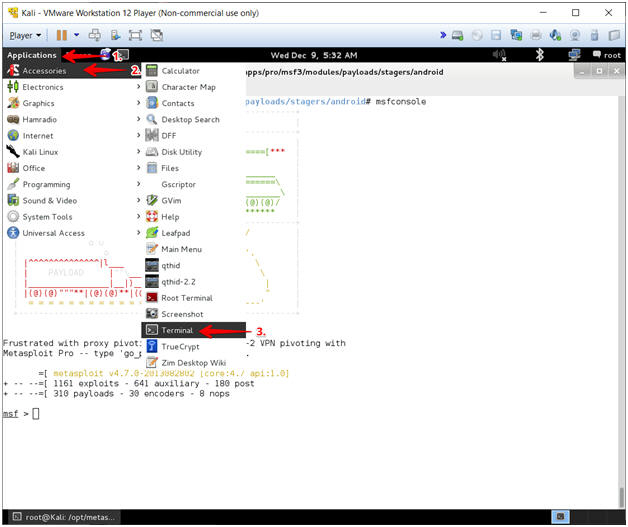
- Start a second Terminal
- Instructions:
- Select Applications
- Select Accessories
- Select Terminal
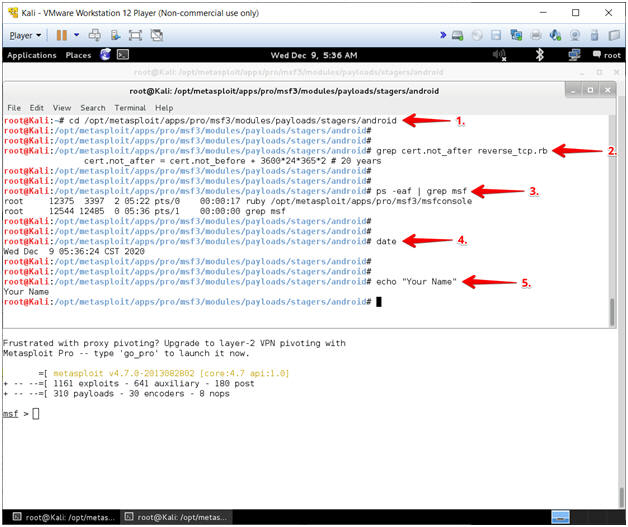
- Proof of Lab
- Instructions:
- cd /opt/metasploit/apps/pro/msf3/modules/payloads/stagers/android
- grep cert.not_after reverse_tcp.rb
- ps -eaf | grep msf
- date
- echo "Your Name"
- Replace the string "Your Name" with
your actual name.
- e.g., echo "John Gray"
-
Proof of Lab
Instructions
- Do a <PrtScn>
- Paste into a word document
- Upload to Moodle
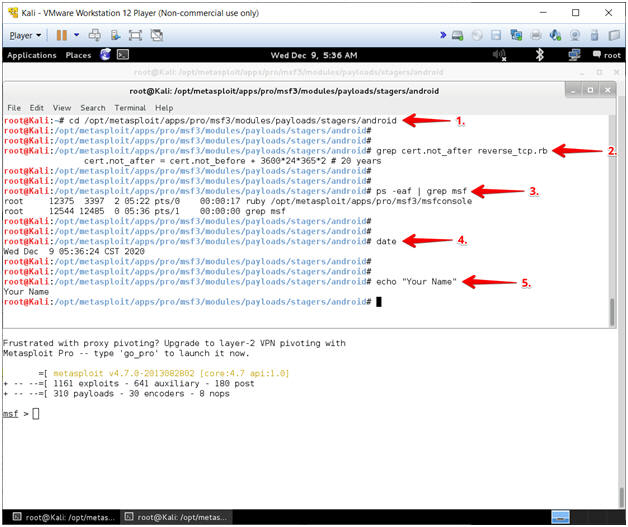
|
 
|