(Fedora: Lesson 14)
{ Setting up tripwire }
| Section 0. Background Information |
- What is tripwire?
- If an attacker gets on to your servers, do you know what they changed?
- Did they modify any of your important files, such as "su" or "cp" or "rm"? How would you know this?
- One answer is the Open Source project Tripwire. This tutorial will cover how to install, configure and maintain Tripwire.
- Open Source Tripwire is a free software security and data integrity tool useful for monitoring and alerting on specific file change(s) on a range of systems.
- Rather than attempting to detect intrusions at the network interface level (as in network intrusion detection systems), Open Source Tripwire detects changes to file system objects.
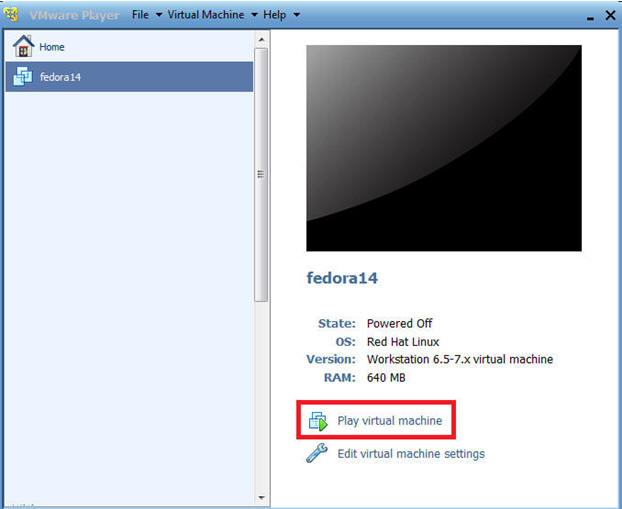
| Section 1. Play the Fedora Virtual Machine |
- Play virtual machine. (See Below)
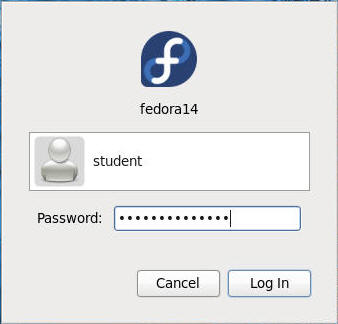
| Section 2. Login to your Fedora14 server. |
- Login As student
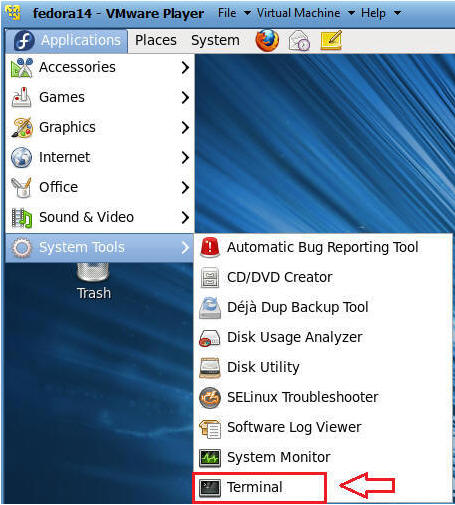
- Start Up A Terminal.
- Applications --> System Tools --> Terminal
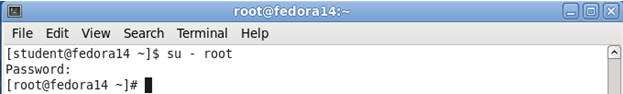
- Switch User to root
- Command: su - root
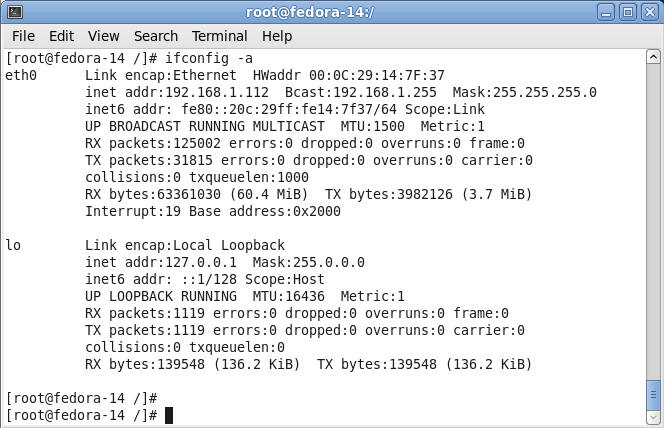
- Determine IP Address and Network Connection.
- Command: ifconfig -a
- Note: In my case, the IP Address is 192.168.1.112.
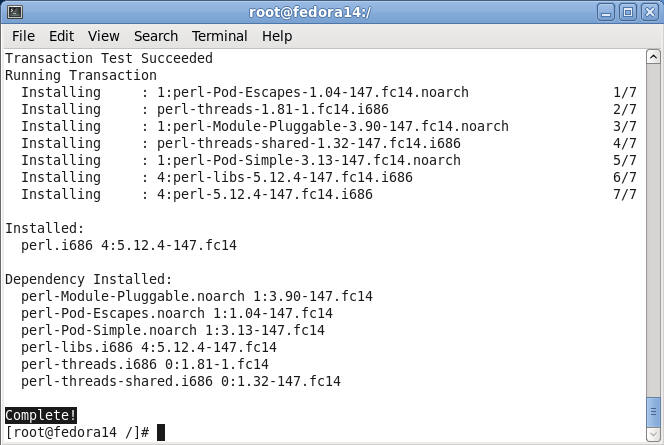
| Section 3. Installing perl |
- Note
- Perl is not a requirement for tripwire.
- However, I will later be using perl to reduce false positives in the /etc/tripwire/twpol.txt file.
- Install tripwire
- Command: yum install "perl"

- Install perl's rpm
- Command: Type "y", and hit enter
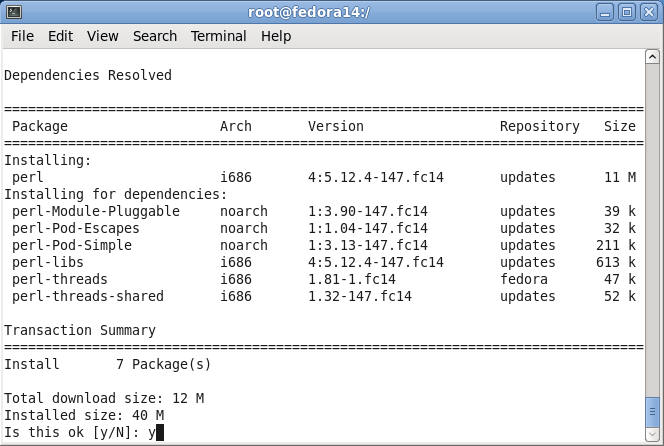
- Verify Installation Results
- Note: Just take note of what is getting installed along with the completion notice.
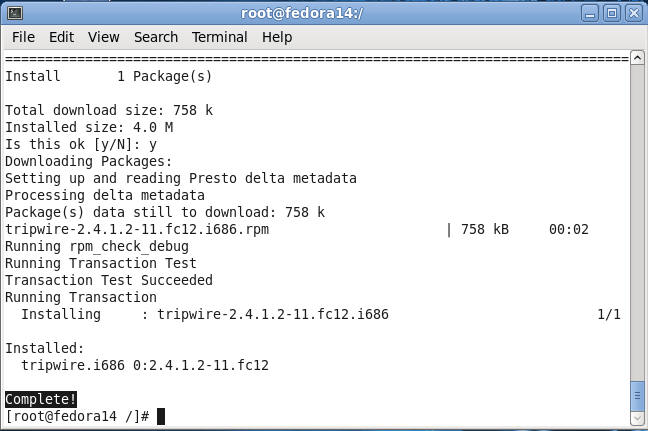
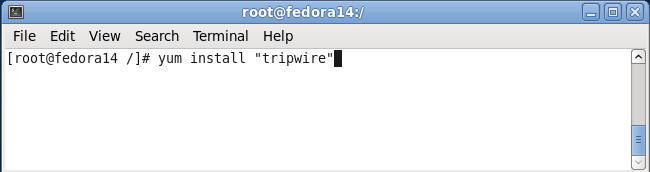
| Section 4. Installing tripwire |
- Install tripwire
- Command: yum install "tripwire"
- Install tripwire's rpm
- Command: Type "y", and hit enter
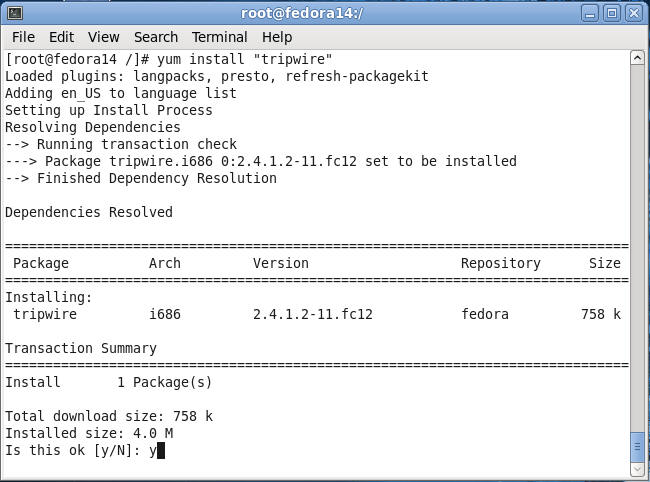
- Verify Installation Results
- Note: Just take note of what is getting installed along with the completion notice.
| Section 5. Initialize tripwire |
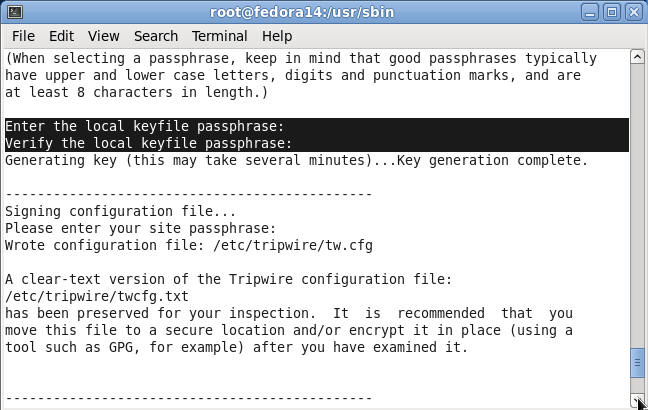
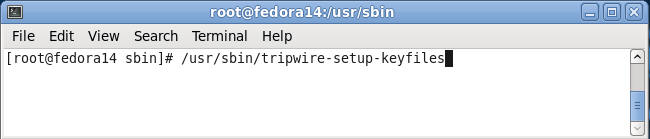
- Setup keyfiles in tripwire
- Command: /usr/sbin/tripwire-setup-keyfiles
- Note:
- During install it will ask you to set up a site keyfile passphrase and a local keyfile passphrase.
- They are used to administer Tripwire, and encrypt the Tripwire policy files.
- This is to protect them against attackers modifying the policies.
- Site keyfile passphrase
- Command: Enter the site keyfile passphrase:
- Note: I recommend using the same password for both site and the local keyfile.
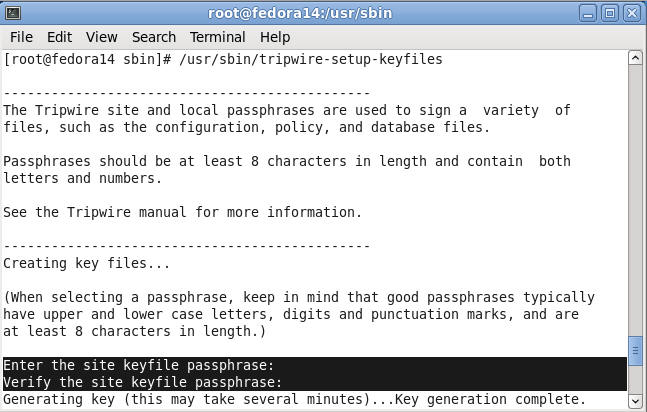
- Local keyfile passphrase
- Command: Enter the local keyfile passphrase
- Note: Use the same password as you did with the site keyfile.
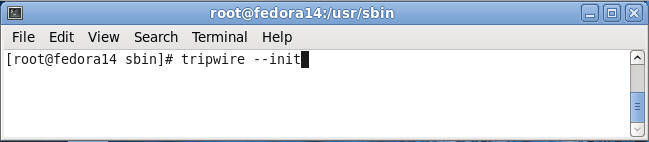
- Initialize Tripwire
- Command: tripwire --init
- Note: You will be required to enter your previously created passphrase.
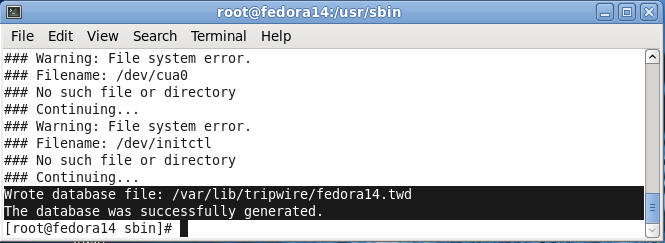
- Verify Results
- Notes:
- The tripwire database file was written to: /var/lib/tripwire/fedora14.twd.
- Also, you should have received a completion message.
- Notes:
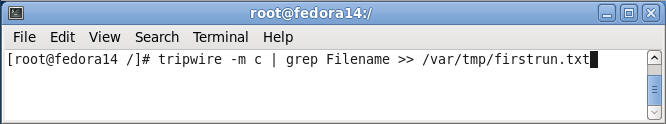
- Run tripwire
- Command: tripwire -m c | grep Filename >> /var/tmp/firstrun.txt
- Note: You will be required to enter your previously created passphrase.
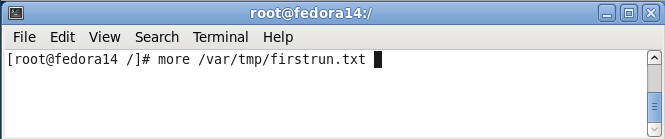
- Looking at the firstrun file.
- Command: more /var/tmp/firstrun.txt
- Note:
- This run should report many out of compliance problems. This is because the default configuration checks many files that may not exist on your server.
- This can be because you didn’t install the software, because you removed software or because you installed it from source. Whatever the reason, we want to turn off these false positives so that we don’t get huge reports each time Tripwire runs.
| Section 6. Reducing False Positives |
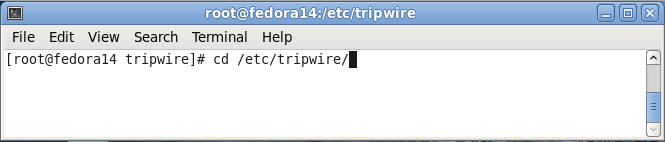
- Navigate to the tripwire configuration
directory
- Command: cd /etc/tripwire
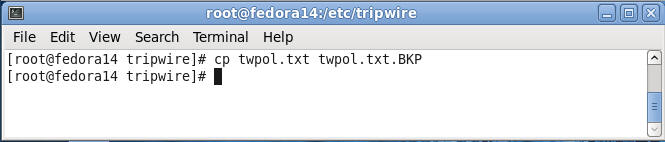
- Make a backup copy of the
- Command: cp twpol.txt twpol.txt.BKP
- Note: When modifying any configuration file, it is always a good idea make a backup file. Although Unix/Linux is a superior Operating System to Windows, it lacks "undo".
- Highlight and copy the code
- Command: Highlight the below code, right-click and copy.
- Pasting Problem Notes: Bring up your web browser inside of Fedora itself, if you are having trouble cutting and pasting from your desktop to Fedora.
- Code:
#!/usr/bin/perl
#Path to tripwire policy backup file
$policy_file = "/etc/tripwire/twpol.txt.BKP";
#Put tripwire policy file into an array
@CONTENT = `cat $policy_file`;
#False Positive Entries we want to ignore
@IGNORE_LIST = `awk '{print \$2}' /var/tmp/firstrun.txt`;
#Open a new file called twpol.txt
open(NEWFILE,">/etc/tripwire/twpol.txt");
#Go through each line in the twpol.txt.BKP file
foreach my $line (@CONTENT)
{
#Chop off the hard return at the end of each line
chomp($line);
#Reset IGNORE_FLAG before each check
my $IGNORE_FLAG = "F";
#Then check the line against the ignore list
foreach my $entry (@IGNORE_LIST)
{
#Chop off the hard return at the end of each line
chomp($entry);
#Compare tripwire line against each ignore list line
if(($line =~ m/\s$entry\s/)&&($line =~ m/-\> \$/))
{
#Setting the FLAG to true means a match was found
$IGNORE_FLAG = "T";
print "[Ignoring]: $line\n";
}
}
if($IGNORE_FLAG eq "F")
{
#Write policy entry to file, if not found in the ignore list
print NEWFILE "$line\n";
}
}
close(NEWFILE);
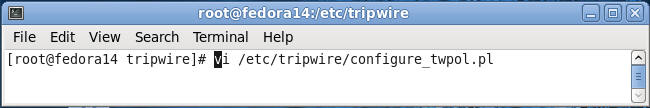
- Create Perl Script
- Command:
- vi /etc/tripwire/configure_twpol.pl
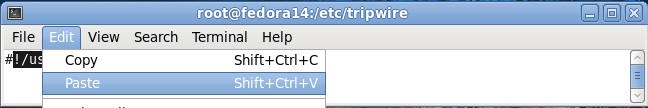
- Command:
- Past the code into a vi session.
- Command:
- Press the "i" key to get into insert mode.
- Edit --> Paste
- Type ":wq" to save and quit.
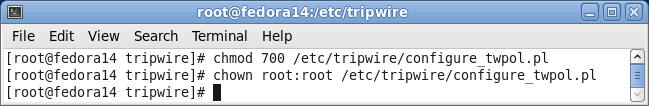
- Command:
- Make the file executable only by root.
- Command:
- chmod 700 /etc/tripwire/configure_twpol.pl
- chown root:root /etc/tripwire/configure_twpol.pl
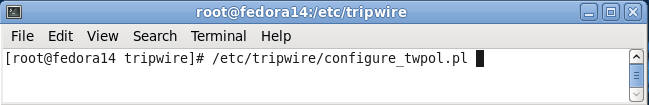
- Command:
- Execute
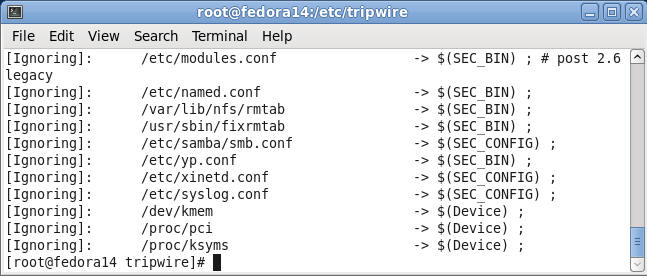
- Command: /etc/tripwire/configure_twpol.pl
- Results
- Notes: After executing the above perl script you will see lines in the twpol.txt that were ignored and not written to the new twpol.txt file.
- Display data collected by sar in multiple
formats.
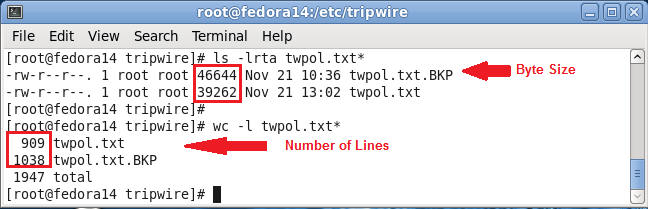
- Command:
- ls -lrta twpol.txt*
- wc -l twpol.txt*
- Notes: Notice the both the bytesize and number of lines of twpol.txt is much less than twpol.txt.BKP
- Command:
| Section 7. Re-initialize tripwire policy |
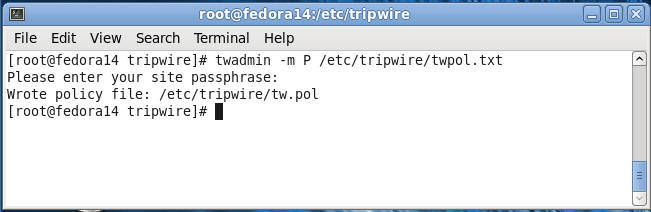
- Re-initialize tripwire policy
- Command: twadmin -m P /etc/tripwire/twpol.txt
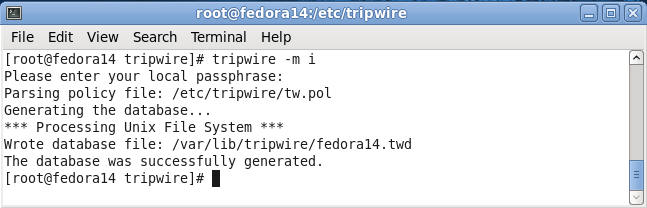
- Re-initialize tripwire database
- Command:
- tripwire -m i
- Enter your local passphrase
- Command:
- Re-initialize tripwire database
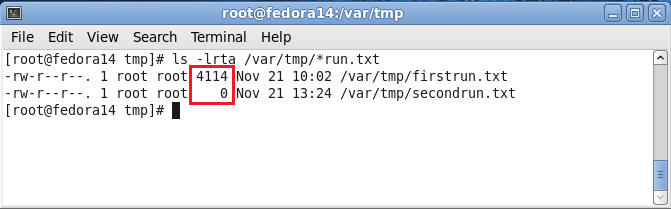
- Command: tripwire -m c | grep Filename > /var/tmp/secondrun.txt
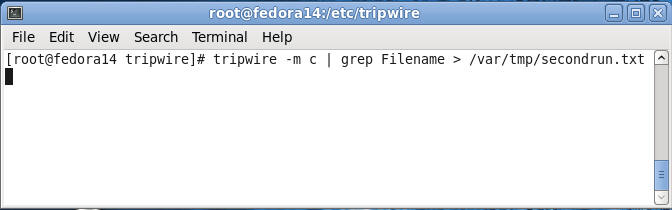
- Compare firstrun.txt to secondrun.txt
- Command: ls -lrta /var/tmp/*run.txt
- Note: Notice the bytesize for secondrun.txt if zero. This means all false positives have been cleaned up.
- Proof of Lab: Do a PrtScn, Paste into a word document and upload to Moodle.
| Section 8. Setting up cron |
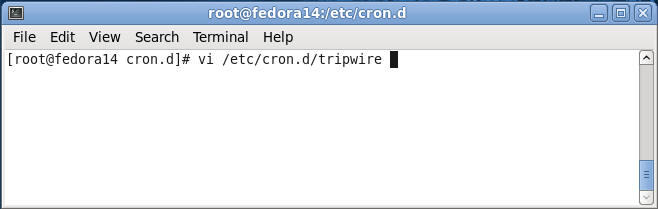
- Create a cron file for tripwire
- Command: vi /etc/cron.d/tripwire
- Adding entries to the tripwire cron file.
- Command:
- Press "i" to go into insert mode
- #Tripwire will run everyday at 2AM server local time
- 0 2 * * * root /usr/sbin/tripwire -m c > /var/tmp/tripwire.`date +%Y%m%d`
- 0 3 * * * root cat /var/tmp/tripwire.`date +%Y%m%d` | mailx -s 'Tripwire Report' example@email.com
- Press the "Esc" key
- Type ":wq" to save and quit.
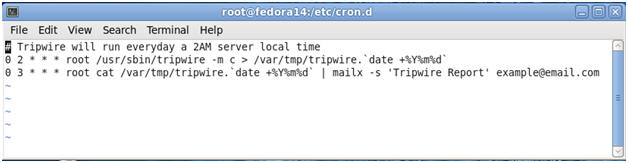
- Command:
| Section: Proof of Lab |
- Cut and Paste a screen shot of Section 7, Step 4 into a word document and upload to Moodle.