(FTK Imager: Lesson 4)
{ Mount Image File, Recover Deleted File }
| Section 0. Background Information |
- What is FTK Imager?
- The FTK toolkit includes a standalone disk imaging program called FTK Imager. The FTK Imager has the ability to save an image of a hard disk in one file or in segments that may be later reconstructed.
- It calculates MD5 hash values and confirms the integrity of the data before closing the files.
- In addition to the FTK Imager tool can mount devices (e.g., drives) and recover deleted files.
- Pre-Requisite
- FTK Imager: Lesson 1: Install FTK Imager
-
FTK Imager: Lesson 2: Create Virtual Hard Drive, Delete File, Recover
File
- Note: This lab is necessary, because you will need to create a Virtual Hard Drive.
-
FTK Imager: Lesson 3: Create Disk Image after Deleting a Picture
- Note: This lab is necessary, because you will need to create an image after deleting a file.
-
Lab Notes
- In this lab we will do the following:
- Mount the Image File.
- View the deleted file.
- Recover the deleted file.
- Compare the MD5 sum of the image after work has been completed to its' original MD5 sum.
- In this lab we will do the following:
- Legal Disclaimer
- As a condition of your use of this Web site, you warrant to computersecuritystudent.com that you will not use this Web site for any purpose that is unlawful or that is prohibited by these terms, conditions, and notices.
- In accordance with UCC § 2-316, this product is provided with "no warranties, either express or implied." The information contained is provided "as-is", with "no guarantee of merchantability."
- In addition, this is a teaching website that does not condone malicious behavior of any kind.
- You are on notice, that continuing and/or using this lab outside your "own" test environment is considered malicious and is against the law.
- © 2012 No content replication of any kind is allowed without express written permission.
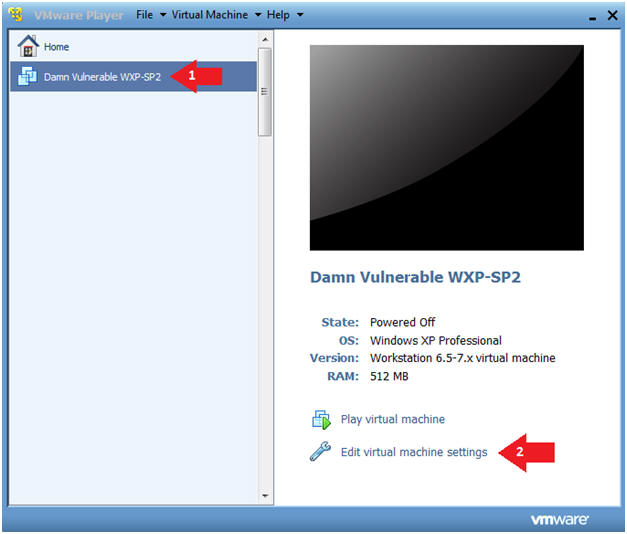
| Section 1: Log into Damn Vulnerable WXP-SP2 |
- Start VMware Player
- Instructions
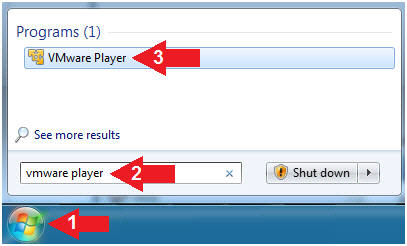
- For Windows 7
- Click Start Button
- Search for "vmware player"
- Click VMware Player
- For Windows XP
- Starts --> Programs --> VMware Player
- For Windows 7
- Instructions
- Start Up Damn Vulnerable WXP-SP2.
- Instructions:
- Click on Damn Vulnerable WXP-SP2
- Click on Edit virtual machine Settings
- Note(FYI):
- For those of you not part of my class, this is a Windows XP machine running SP2.
- Instructions:
- Edit Virtual Machine Settings
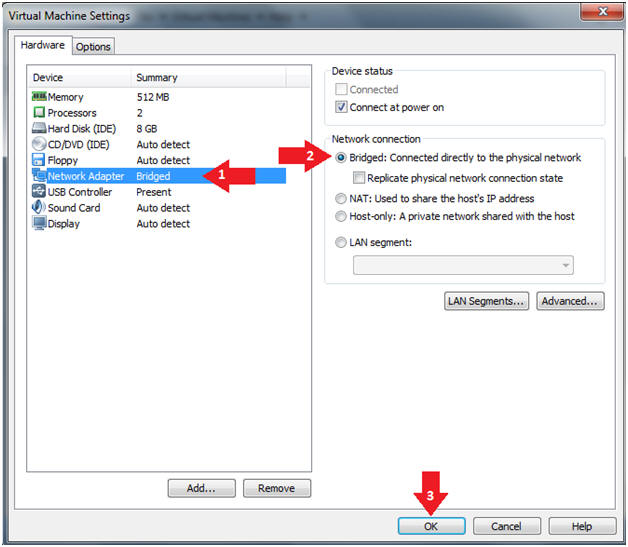
- Instructions:
- Click on Network Adapter
- Click on the Bridged Radio button
- Click on the OK Button
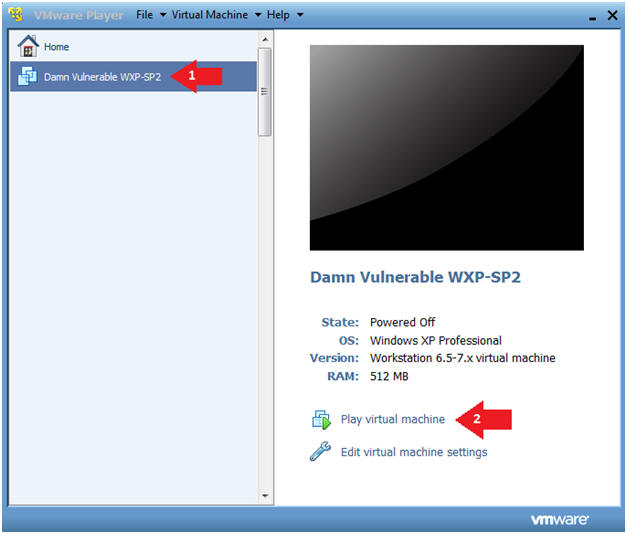
- Instructions:
- Play Virtual Machine
- Instructions:
- Click on Damn Vulnerable WXP-SP2
- Click on Play virtual machine
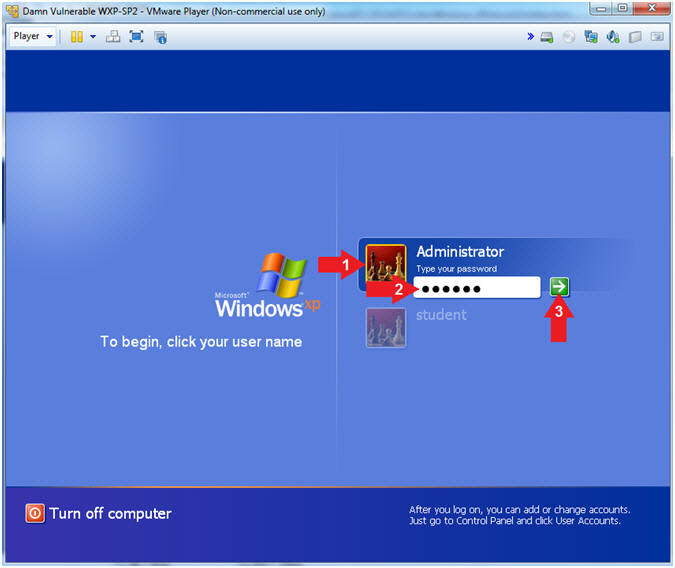
- Instructions:
- Logging into Damn Vulnerable WXP-SP2.
- Instructions:
- Click on Administrator
- Password: Supply Password
- Press <Enter> or Click the Arrow
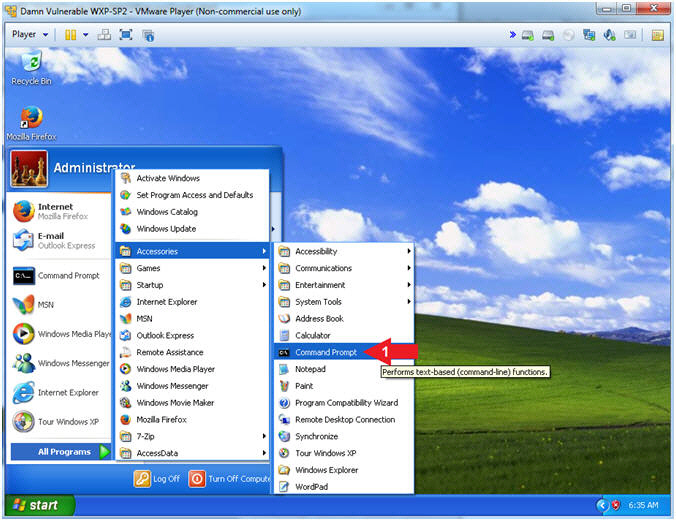
- Instructions:
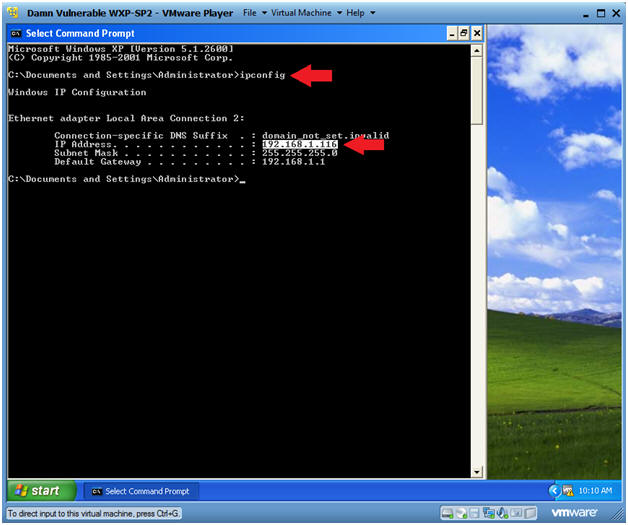
- Open a Command Prompt
- Instructions:
- Start --> All Programs --> Accessories --> Command Prompt
- Instructions:
- Obtain Damn Vulnerable WXP-SP2's IP Address
- Instructions:
- ipconfig
- Note(FYI):
- In my case, Damn Vulnerable WXP-SP2's IP Address 192.168.1.116.
- This is the IP Address of the Victim Machine that will be attacked by Metasploit.
- Record your Damn Vulnerable WXP-SP2's IP Address.
 .
.
- Instructions:
| Section 2: Start FTK Imager |
- Start FTK Imager
- Instructions:
- Click on the Start Button
- All Programs --> AccessData --> FTK Imager --> FTK Imager
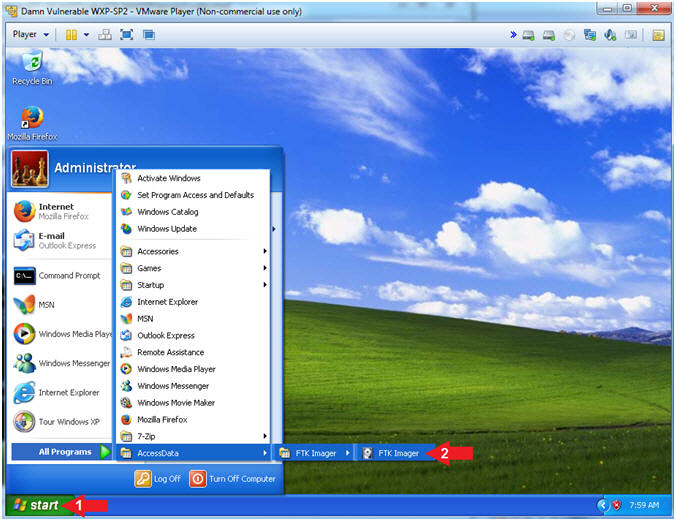
- Instructions:
| Section 3: Mount Image |
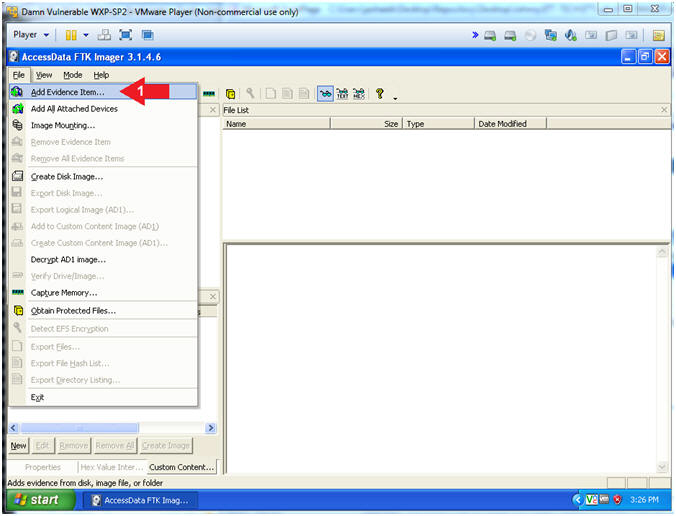
- Add Evidence
- Instructions:
- File --> Add Evidence Item...
-
- Instructions:
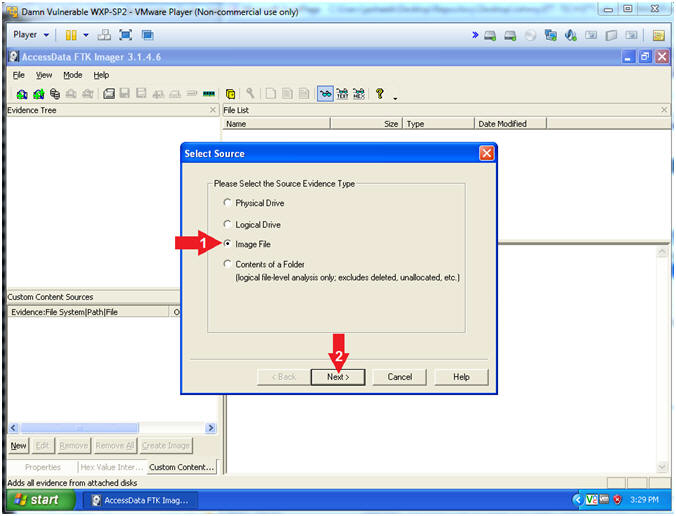
- Select Source
- Instructions:
- Click on the Image File radio button
- Click the Next Button
- Instructions:
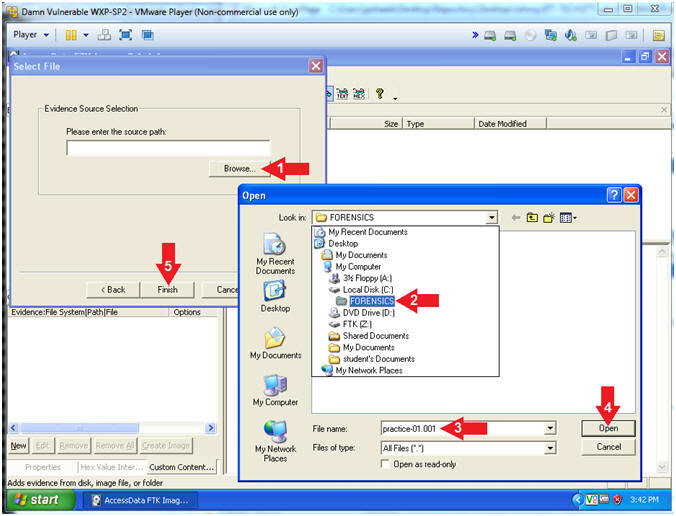
- Select File
- Instructions:
- Click the Browse Button
- Navigate to C:\FORENSICS
- Select practice-01.001
- Click the Open Button
- Click the Finish Button
- Instructions:
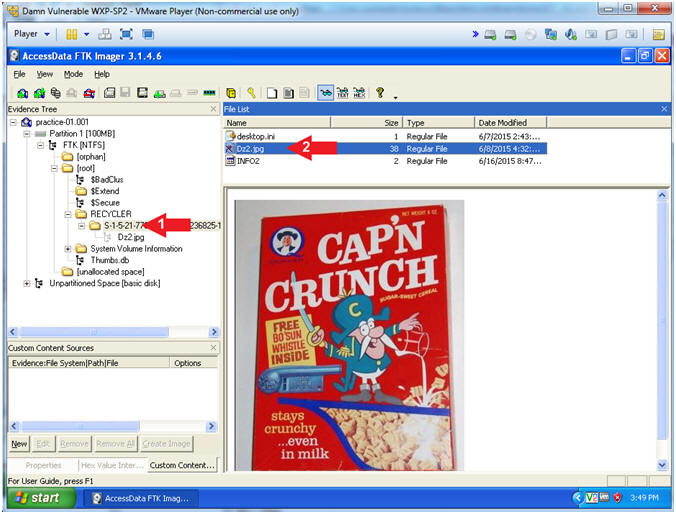
| Section 4: View Deleted Image |
- View Deleted File(s) in the Recycler
- Instructions:
- Navigate to practice-01-001 --> Partition 1
--> FTK[NTFS] --> [root] --> RECYCLER --> RECYCLER SUBDIR
- The RECYCLER SUBDIR Directory name varies
- Click on the jpg file if it exists.
- The naming convention of existing jpg's also varies.
- Navigate to practice-01-001 --> Partition 1
--> FTK[NTFS] --> [root] --> RECYCLER --> RECYCLER SUBDIR
- Instructions:
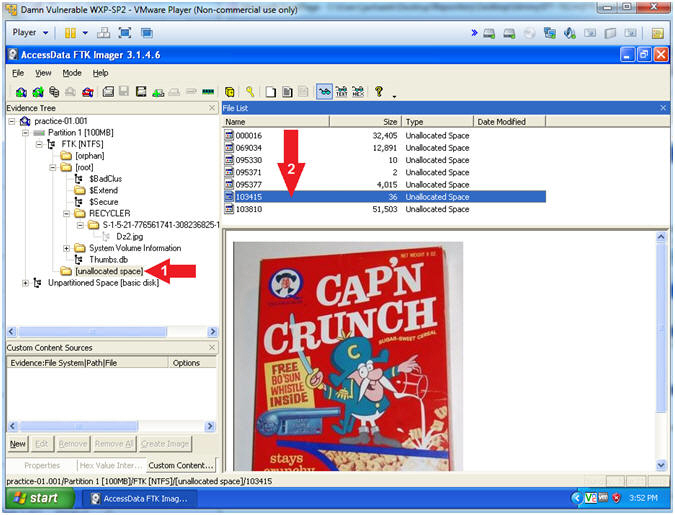
- View Deleted File(s) in [unallocated space]
- Instructions:
- Navigate to practice-01-001 --> Partition 1 --> FTK [NTFS] --> [root] --> [unallocated space]
- Scroll through all the files until you see the Captain Crunch Picture
- Instructions:
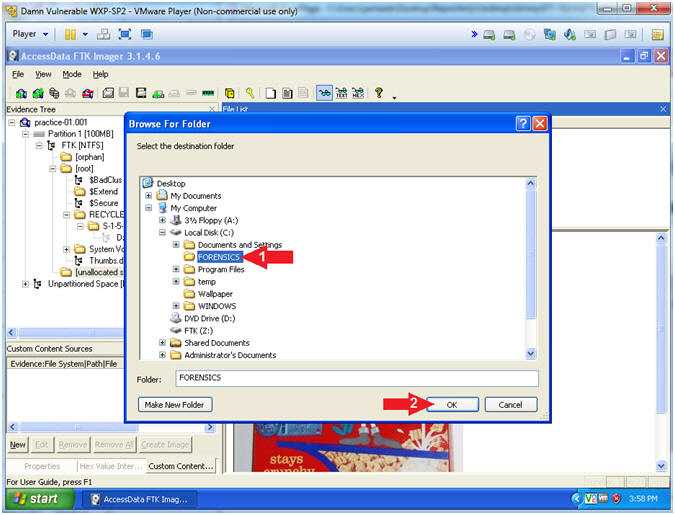
| Section 5: Recover Deleted Image |
- Export File
- Instructions:
- Right Click on the file that contains the picture
- Select Export Files...
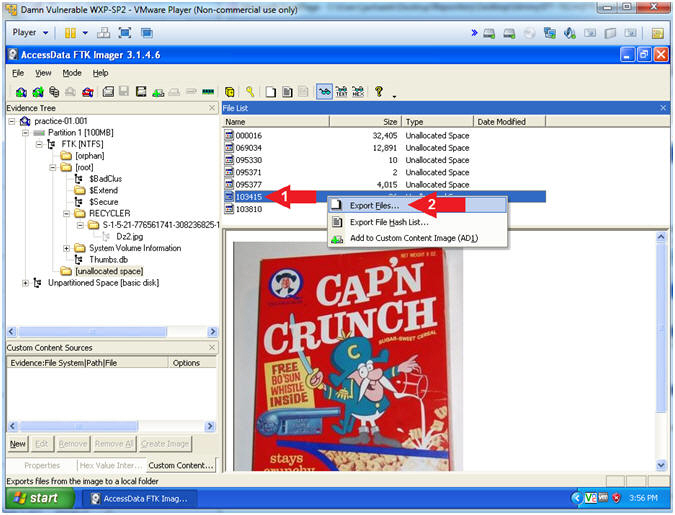
- Instructions:
- Select the destination folder
- Instructions:
- Navigate to C:\FORENSICS
- Click the OK Button
- Instructions:
- Export Results
- Instructions:
- Click the OK Button
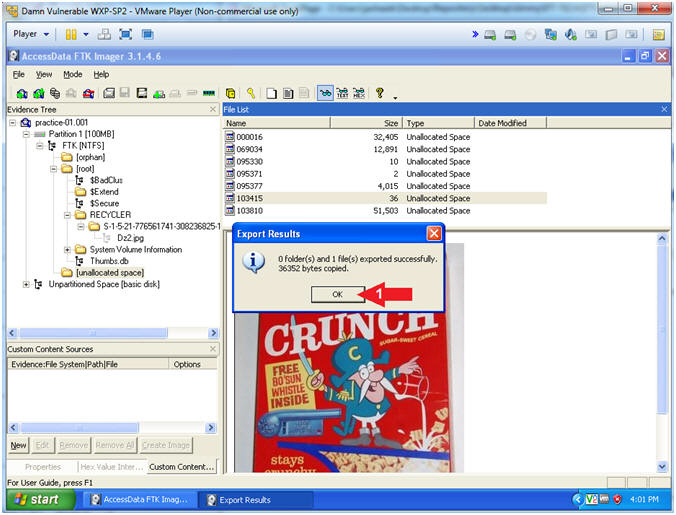
- Instructions:
| Section 6: View Recovered Picture |
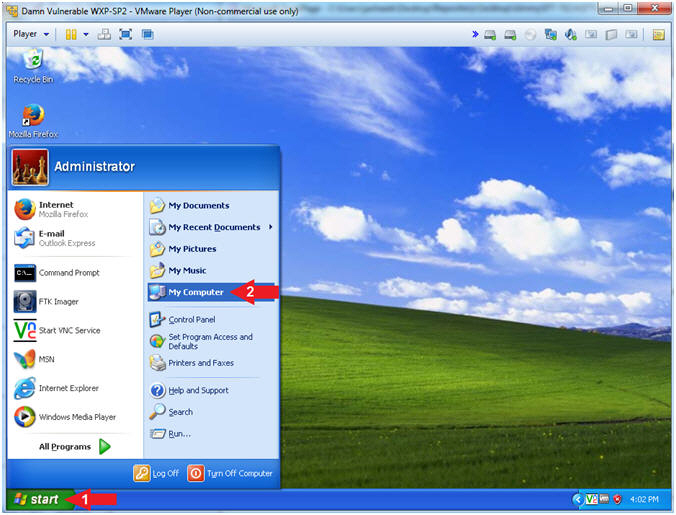
- Open My Computer
- Instructions:
- Click the Start Button
- Click on My Computer
-
- Instructions:
- Rename File
- Instructions:
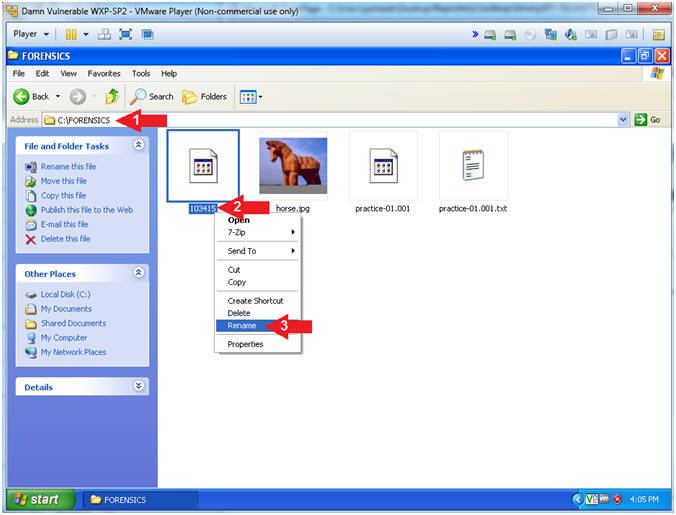
- Navigate to C:\FORENSICS
- Right Click on the filename that
contain all numbers
- In my case the filename is 103415. In your case, it will probably be named differently.
- Click Rename
- Instructions:
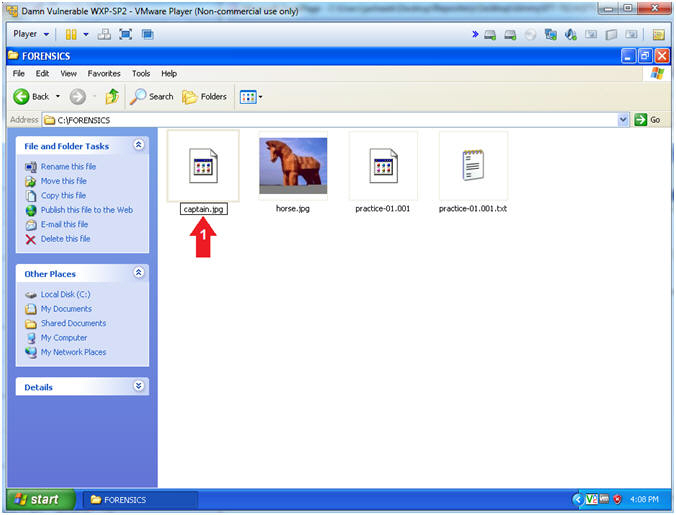
- Name File
- Instructions:
- Rename file to "captain.jpg"
- Instructions:
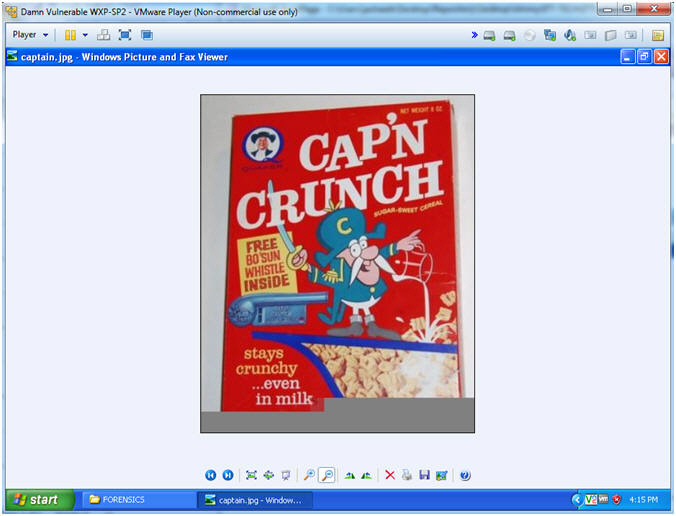
- Open File
- Instructions:
- Right Click "captain.jpg"
- Open With --> Windows Picture and Fax Viewer
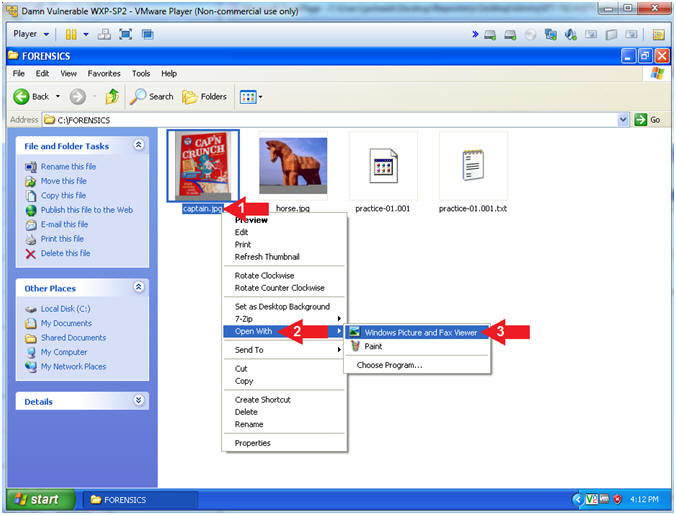
- Instructions:
- View File
- Note(FYI):
- CAP'N Crunch was a h4x0r.... nice whistle.
- Note(FYI):
| Section 7: Calculate Post MD5 Hash |
- Verify Image
- Instructions:
- Right Click practice-01-001
- Click on Verify Drive/Image
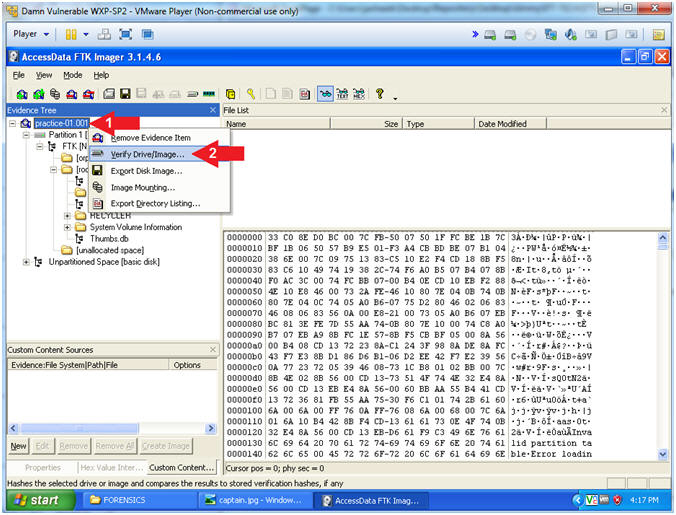
- Instructions:
- Drive/Image Verify Results
- Instructions:
- Copy the last 4 characters of your MD5
Hash
- In my case, it is 6e9c.
- Do Not Click the Close Button
- Copy the last 4 characters of your MD5
Hash
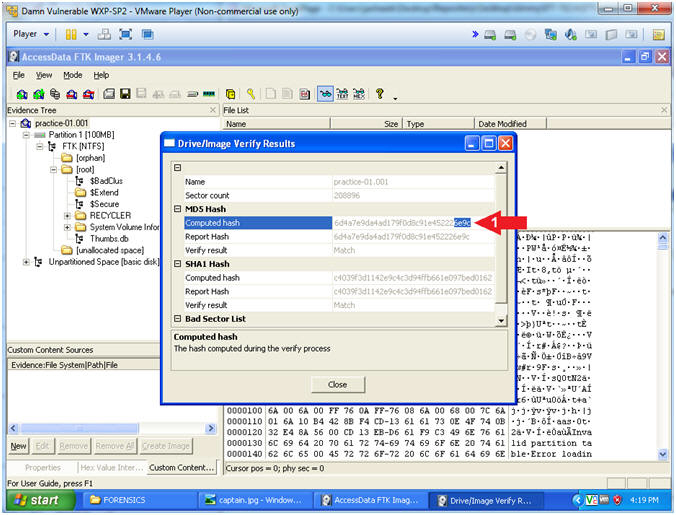
- Instructions:
| Section 8: Proof of Lab |
- Open a Command Prompt
- Instructions:
- Start --> All Programs --> Accessories --> Command Prompt
- Instructions:
-
Proof of Lab
- Instructions:
- cd C:\FORENSICS
- type practice-01.001.txt | findstr
"e358c"
- Replace "e358c" with the string you obtained from (Section 7, Step 2)
- This step verifies that MD5 Hash did not change since the image was first created.
- date /t
- echo "Your Name"
- This should be your actual name.
- e.g., echo "John Gray"
-
Proof of Lab
Instructions
- Press both the <Ctrl> and <Alt> keys at the same time.
- Do a <PrtScn>
- Paste into a word document
- Upload to Moodle
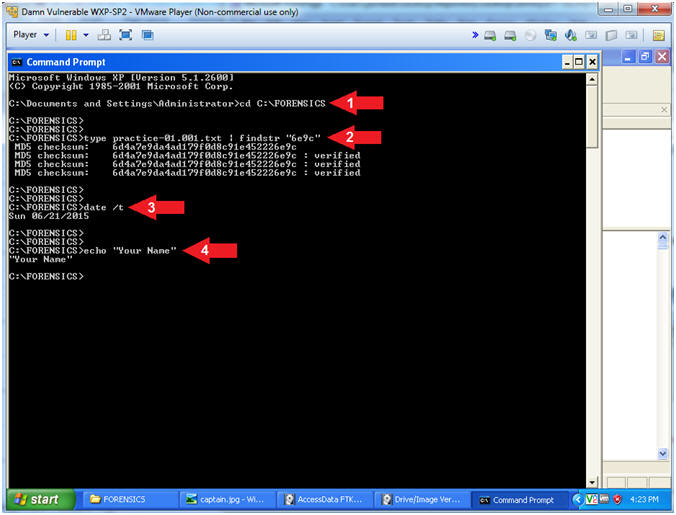
- Instructions: